

Blog
insight and research in cybersecurity with swIDch Blog.
Popular

Approval has long been treated as a proxy for control. If access is approved, it is assumed to be...

At a large industrial site, a contractor needed temporary access to a controller to complete...

At a large manufacturing plant in Northern Europe, a routine maintenance task nearly became a...

For many OT organisations, Passwordless still feels abstract. The concept is attractive — fewer...

For years, Passwordless has been discussed as a modern authentication approach — faster logins,...

Industrial operators step into 2026 with clearer mandates, tighter regulations, and rising cyber...

2025 made one truth uncomfortably clear: the biggest weaknesses in OT security no longer sit...

The OT and critical infrastructure incidents we witnessed throughout 2025 showed, with unusual...

2025 was marked by a series of real-world OT and infrastructure incidents across Europe and North...
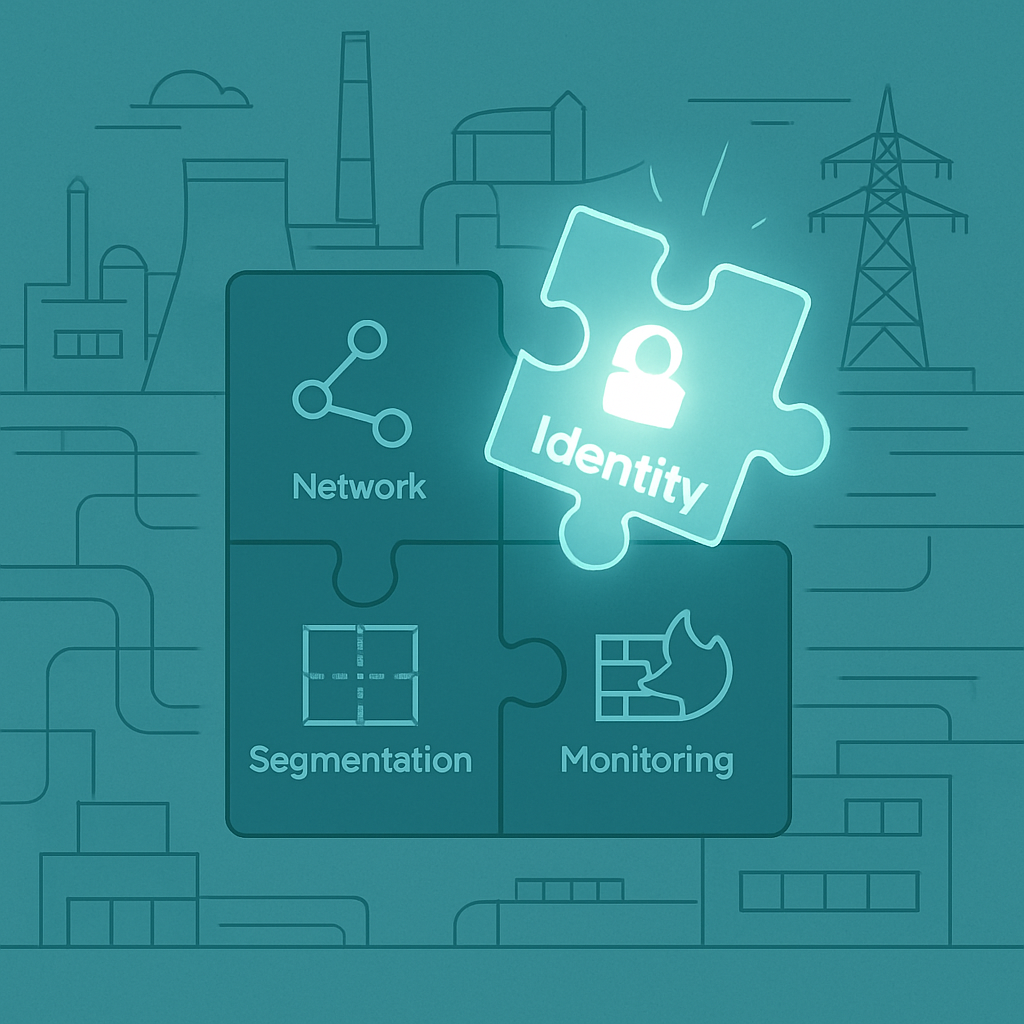
Even after a year filled with operational technology (OT) security investments, audits, and...
Looking to stay up-to-date with our latest news?
