

Blog
insight and research in cybersecurity with swIDch Blog.
Popular

In 2026 countless industrial organisations are pouring billions into threat detection solutions...

The recent move by Bulgaria to codify the EU NIS2 Directive into national law has established a...
%20How%20the%20OT%20Security%20Crisis%20Is%20Creating%20a%20Coverage%20Cliff%20in%20Cyber%20Insurance.png)
As industrial organisations enter the second quarter of 2026 a fundamental shift in the cyber...

In 2026 downtime in the industrial sector is no longer viewed as a mere operational hurdle but as...
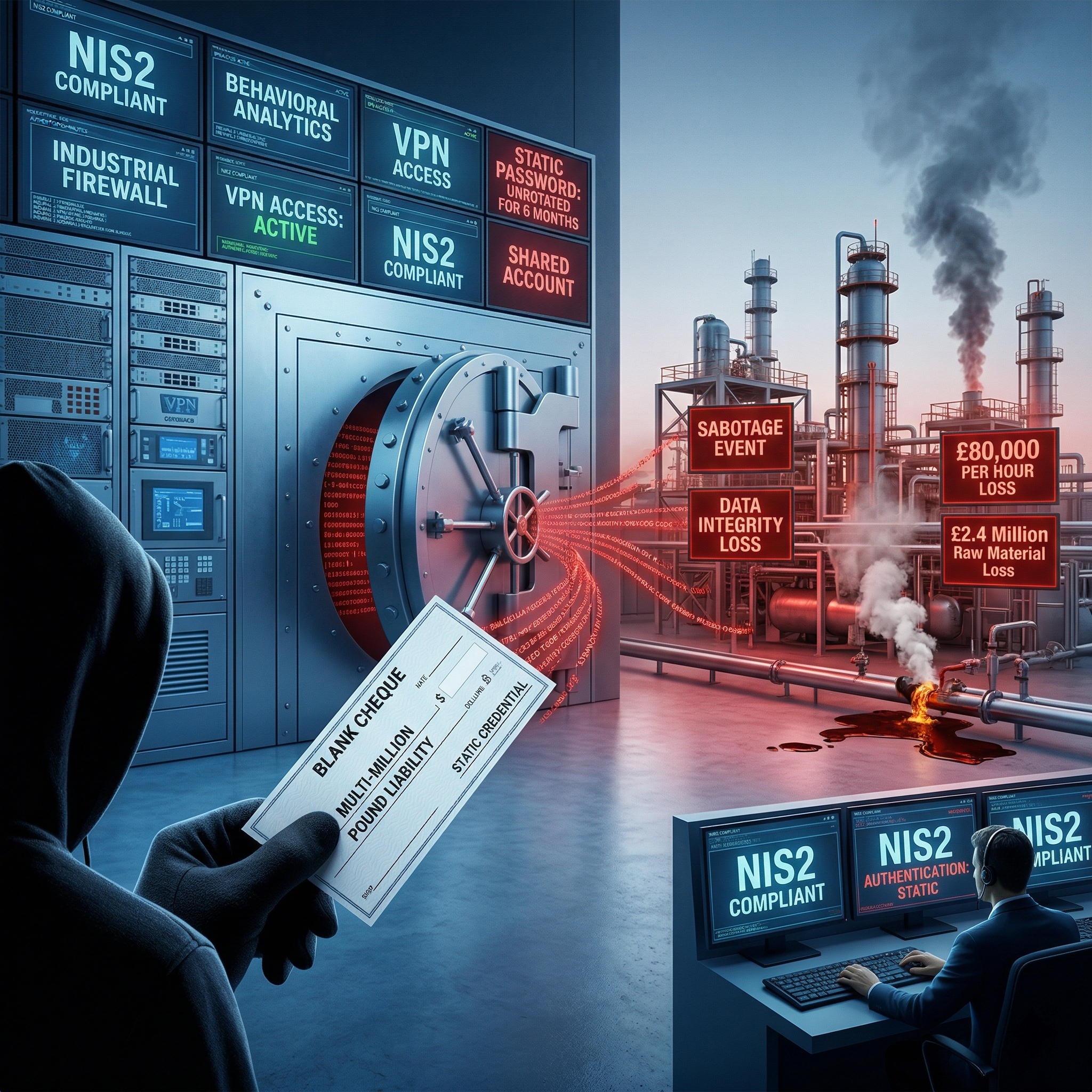
In 2026 the reliance on static passwords within Operational Technology is no longer just a...
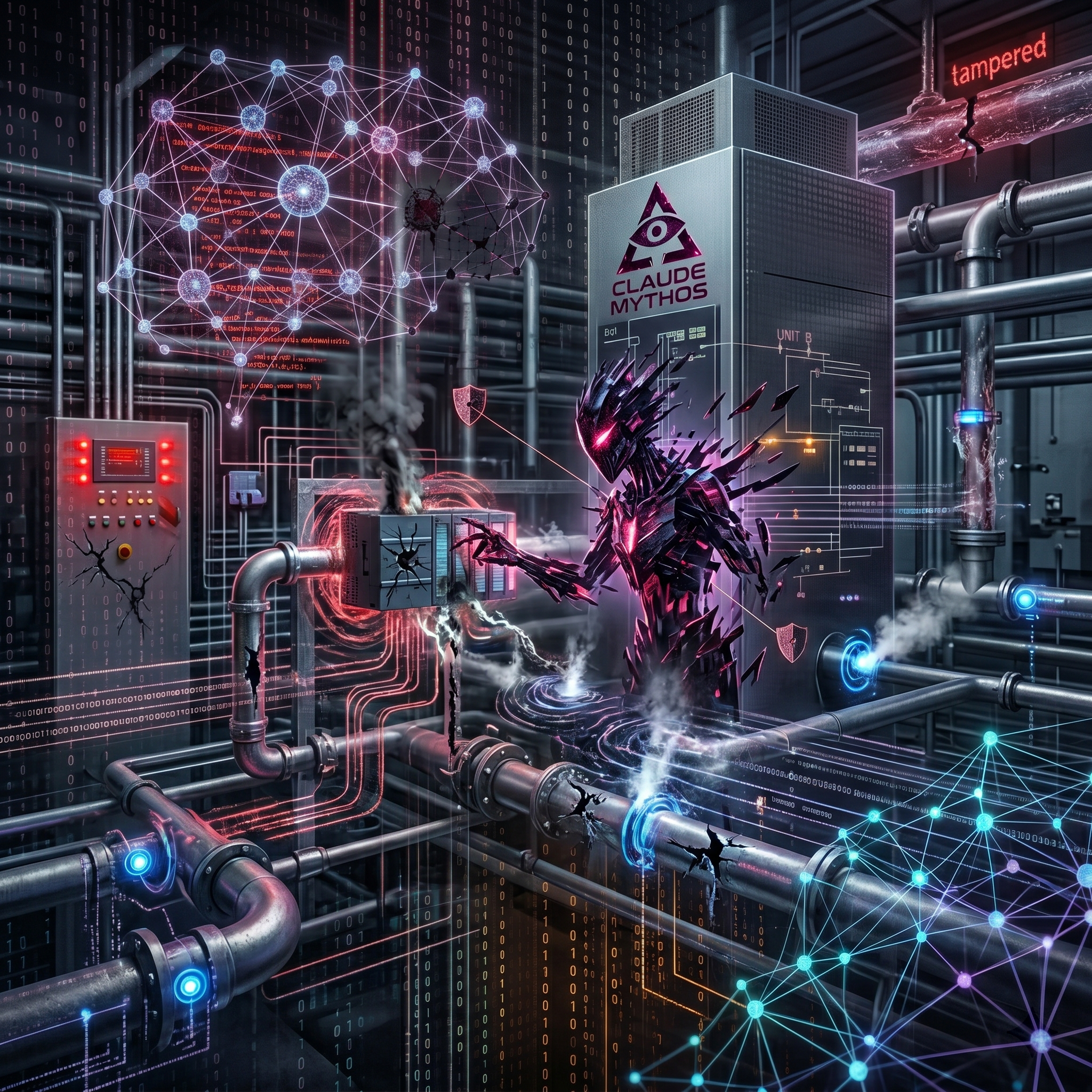
Anthropic's Claude Mythos marks a definitive shift in the cybersecurity landscape. We are no...

The recent Cybersecurity Advisory (AA26-097A) issued by the US Cybersecurity and Infrastructure...

As industrial organisations enter the second quarter of 2026 a fundamental shift in the cyber...
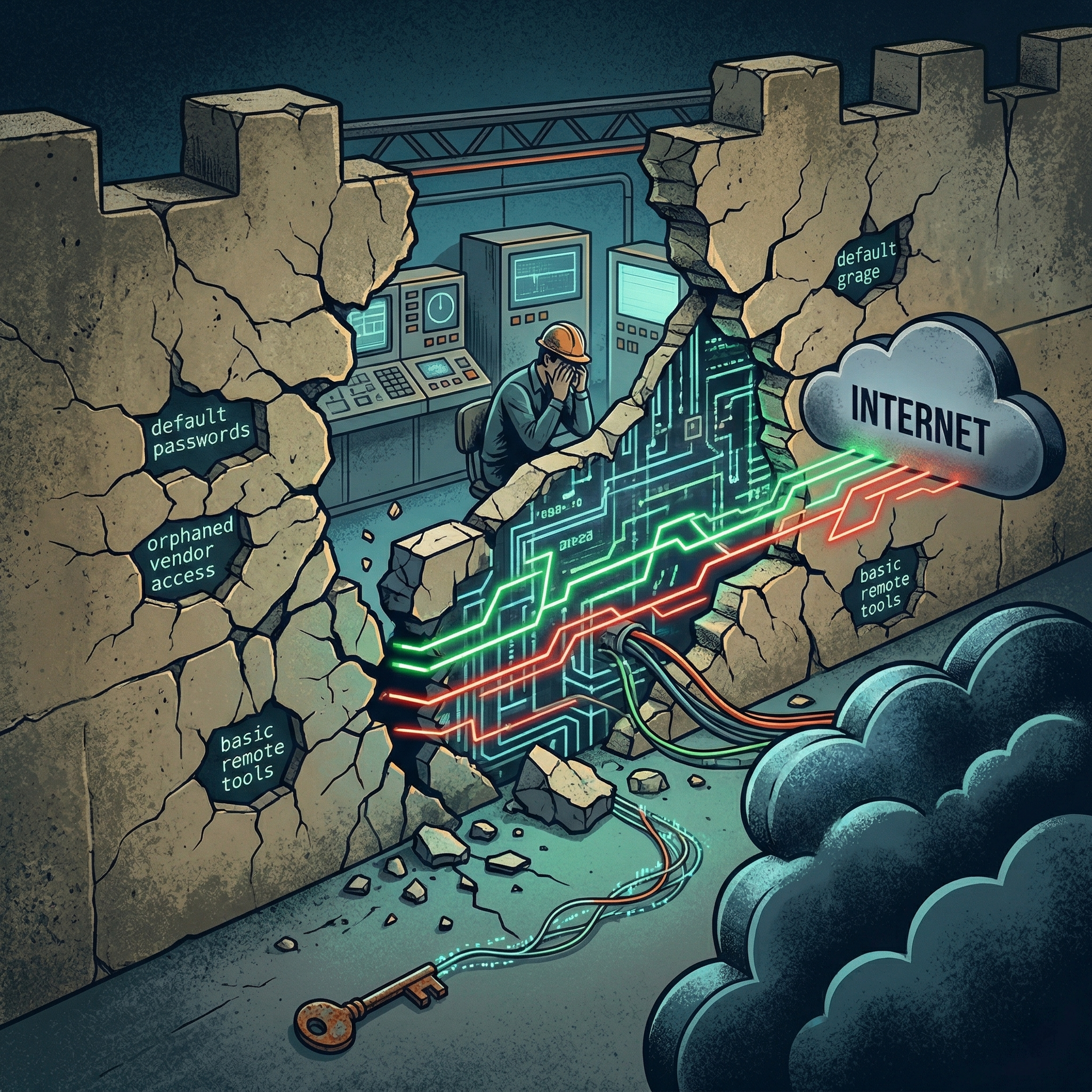
The most enduring comfort in industrial security has always been the concept of physical...

A startling figure has emerged from recent global OT security research that should keep every...
Looking to stay up-to-date with our latest news?