

HomeNet OTAC
Robust user and device authentication for home networks, a hub for home smart
devices and a huge smart platform unto itself.
Pain points
Armed with a huge network and various high-tech systems, modern apartments are regarded as the most popular future living spaces in the world. According to Eurostat, as of 2019, 46.1% of residents in the European Union lived in apartments, with Spain (65%), Switzerland (62%), Greece (59%), Germany (56%) and Italy (53%). This means more than half of the total population lives in apartments. In the United States, where the proportion of single-family homes is 70%, the proportion of apartments in large cities such as New York is as high as 24%. According to the results of the '2020 Housing Status Survey' by the Ministry of Land, Infrastructure and Transport, the apartment occupancy rate among all households in Korea was 51.1% as of 2019. As the proportion of apartment dwellers increases, various security breaches are also increasing. In particular, due to the nature of apartments that share a common network and system such as CCTV and parking systems, hacking of one household can spread to the entire complex, requiring substantial intervention.

Smart home cyber attacks on the rise
Although large apartment complexes boast a network size comparable to that of corporate networks, they are easy targets for cyberattacks because they do not distinguish between strong authentication and access rights in the way corporate networks do. According to one study, a whopping 12,000 cyber-attacks were carried out on a single smart home system in a week, most of which were malicious approaches targeting routers, wireless cameras, printers, etc. In Korea, as it was confirmed that private videos recorded on the wall pad are being sold through the dark web as a result of malicious access by hackers through devices with a relatively weak user authentication process, countermeasures against cyber threats are required.
Compliance issues in accordance with relevant laws
Numerous cyber threats such as deep fakes, phishing attacks, malware, and ransomware are now not only hacking home network security cameras, threats to common spaces, door locks, and temperature control systems to infiltrate private residential space are also an issue. Unauthorized access and intrusion are also potential risk factors, and as a result new laws are emerging. In Europe, the focus is mainly on the imposition of manufacturers' security obligations such as the ban on basic passwords on smart devices and equipment, while in Asian countries including Korea, structural solutions such as the application of encryption technology are being actively discussed.
Solutions
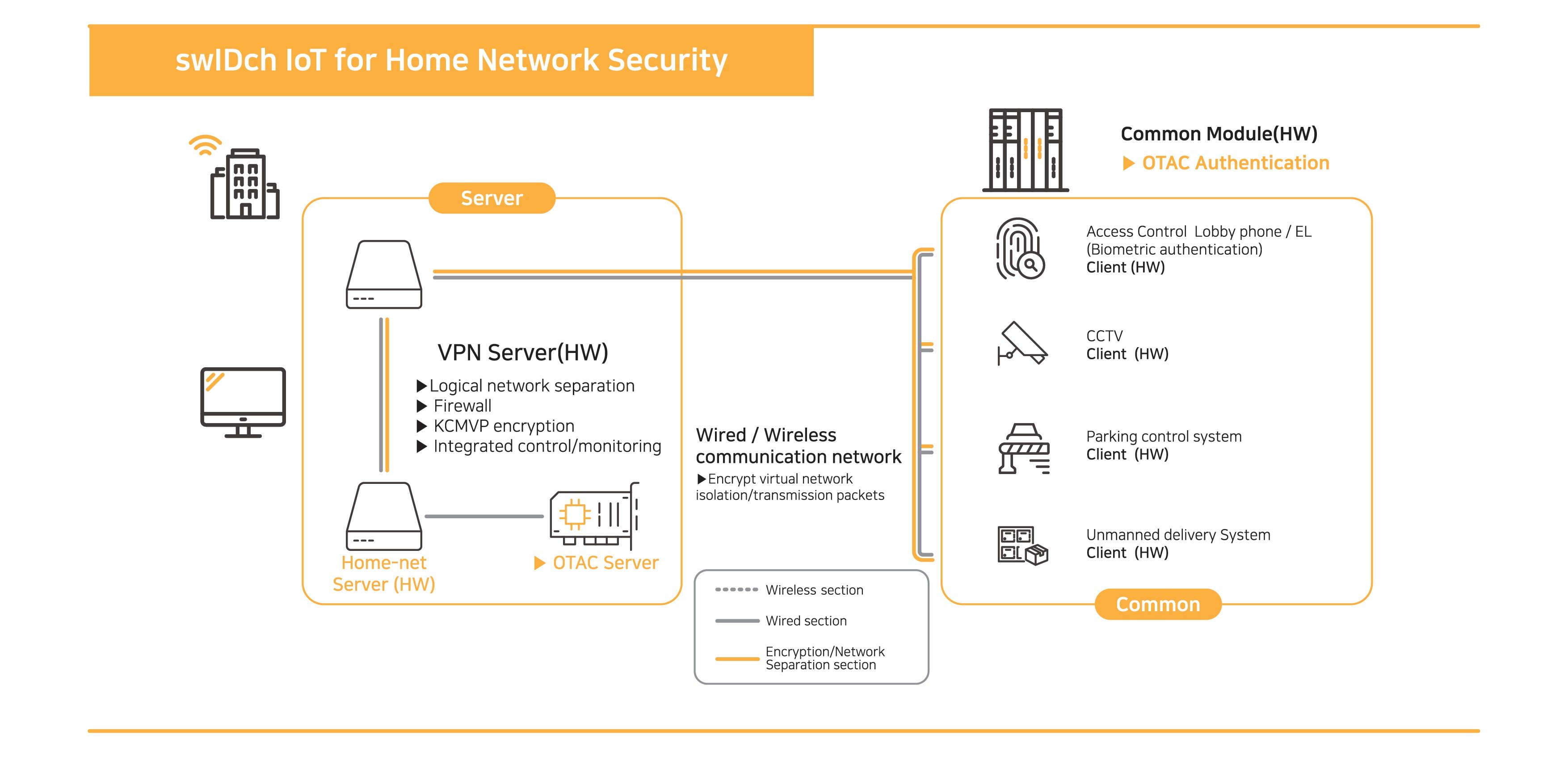
swIDch HomeNet OTAC neutralizes the intrusion itself by converting the user and device authentication process, which is the gateway to external threats to the home network, into a dynamic code that constantly changes instead of a fixed value. It operates a strong security network by verifying normal access not only for devices connected to the home network system by wire, but also for remote access through a user's mobile device. In particular, in conjunction with the hardware-based encryption module, it forms a super-secure security system environment.
Block external threats through simple authentication and verification
swIDch verifies the OTAC generated by the device during encrypted communication connection between the device and the server, and forms an encrypted communication channel if it is determined to be a device within a normal home network. OTAC is transmitted periodically even during the encrypted communication channel connection to determine whether to maintain the encrypted communication channel. In particular, swIDch ensures a secure connection without compromising user convenience by verifying through OTAC whether both wired and wireless access are from normal devices of the registered user.
Proven hardware encryption module linkage
swIDch’s HomeNet OTAC works in conjunction with a proven VPN module that satisfies compliance standards to authenticate user devices and configure a secure communication channel for each device. As the authentication process is performed using a one-way dynamic authentication code method, rather than the ID and PW method mainly used in existing home network systems, it’s not only free from compliance issues, it’s also possible to build a stronger security infrastructure by linking with the hardware encryption module.
Benefits
When the smart home, which is transforming into a gigantic Internet of Things, is free from cyber threats, it will be reborn as a space for production and consumption of derivative services linked to public data, beyond simply a living space, as well as a base for a smart city, a future urban structure. swIDch provides a safer and more convenient smart home environment by freeing the home networks from cyber threats that are increasingly stronger and more intelligent.
Residents' housing satisfaction and space value increase
swIDch’s HomeNet OTAC provides safe access control of common spaces and infrastructure in apartment complexes, as well as the implementation of a safe smart home system for each household, enabling residents to comfortably experience a smart home environment without worrying about cyber threats. This in turn adds to the overall value of the property and/or space.
Establishment and advancement of intelligent residential space
swIDch’s HomeNet OTAC provides a more intelligent and advanced smart home network environment by interworking with logical access management and physical access control systems. Applied to the home network control server, even when logging in to the internal network separated from the Internet network, login is possible by simply entering the dynamic OTAC generated on the user's smartphone in real time in one direction (un-directionally). If you have a mobile app embedded with OTAC, an authentication code can be generated and used as an access key even in an unstable communication/network environment. The physical access card embedded with the OTAC Applet enables control of common and individual entrance doors only by tapping the card on the door. Read more >
Contact us today
Why swIDch
that provides all of the following features, tested and substantiated
by the University of Surrey technical report
sufficient to IDENTIFY user
and AUTHENTICATION
off-the-network environment
Single-step identification and authentication with the code alone. Include our biometric option and get single-step MFA. Vastly improved UX by removing steps.
OTAC is a dynamic code, which means the code is constantly changing. Eliminates all use of static information. Forget usernames and passwords forever. Vastly reduced workload for IT helpdesks.
No network connection required for generating OTAC, enabling uninterrupted use no matter where you are. No more waiting for additional tokens/OTPs and no need for heavy public key infrastructure (PKI).
Highly configurable code parameters and lightweight SDK/applet means wide range of deployment options on many devices across multiple sectors.