

Drone OTAC
patented OTAC technology
Pain points
The Drone industry is rapidly developing and impacting our daily lives in numerous and innovative ways. It has the ability to change our lives in for the better in ways which are hard to comprehend. However, with this innovation comes the potential negative impact of security breaches and exploitation from external rogue sources. swIDch’s patented technology enhances drone security solutions to keep the device and product in secured modes at the same time, with simple use cases for many different purposes.
As it stands, there are the 3 main challenges that the drone industry and/or drone market is facing today.
- • hijacking issues
- • identification issues
- • compliance issues
Security: Hijacking
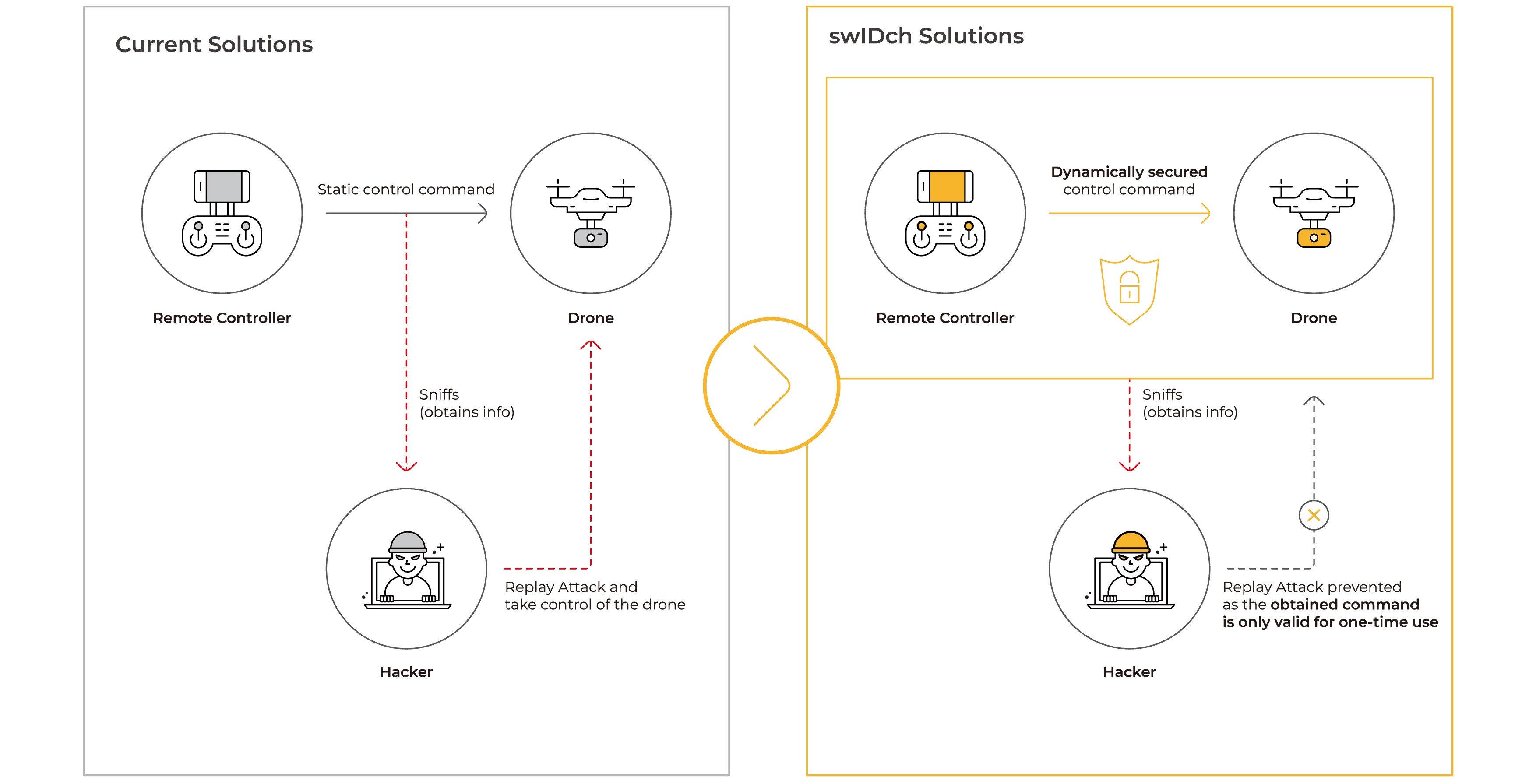
Drone communications with remote controllers are often encrypted, but the encrypted codes are often the same (i.e. static), which makes it a preferred and easy target for hijacking. In military drones, extra hardware, CMVP (Cryptographic Module Validation Program) is installed in drones to validate the security level in communications. Small commercial drones on the other hand often rely on the existing encrypted communication methods which are relatively easy to hijack.


Safety: Identification
Drones are small, fast, and relatively difficult to detect in comparison to a flying jet. When multiple aircrafts, both manned and unmanned, are flying, each device needs to identify and communicate with each other
to guarantee safety and mission success. This is why there is need for an identification system for drones and its operators. The economic cost of an unidentified drone near an airport is 500,000 euros for every 30 mins an airport is stopped from operating.
Regulation: Compliance issues
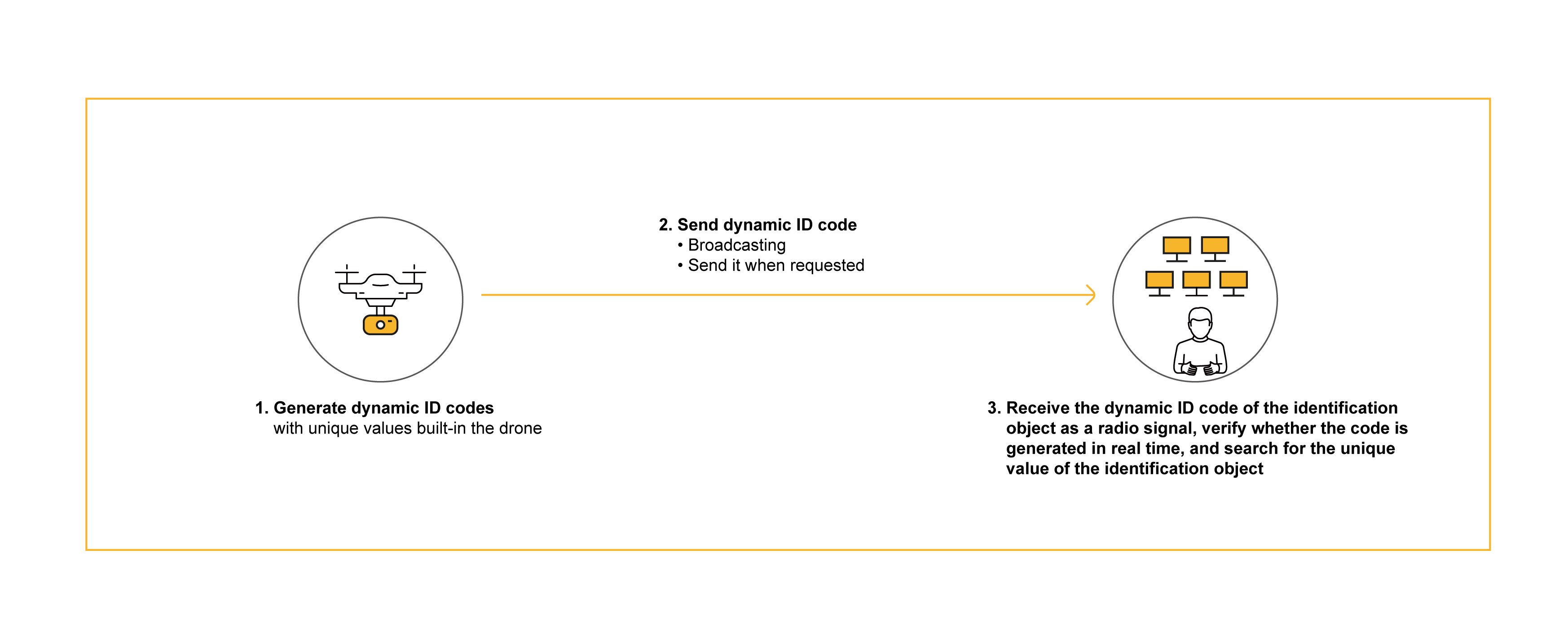
Remote ID is a new regulation introduced by the FAA and it is the “ability of a drone in flight to provide identification and location information that can be received by other parties”, such as law enforcement. To comply with this upcoming regulation, drone manufacturers are having to implement a solution to embed identification capabilities on drones in accordance with the standards given by the FAA. The drone pilots/operators must also register themselves with the FAA before they can legally fly the drones.
The Solution
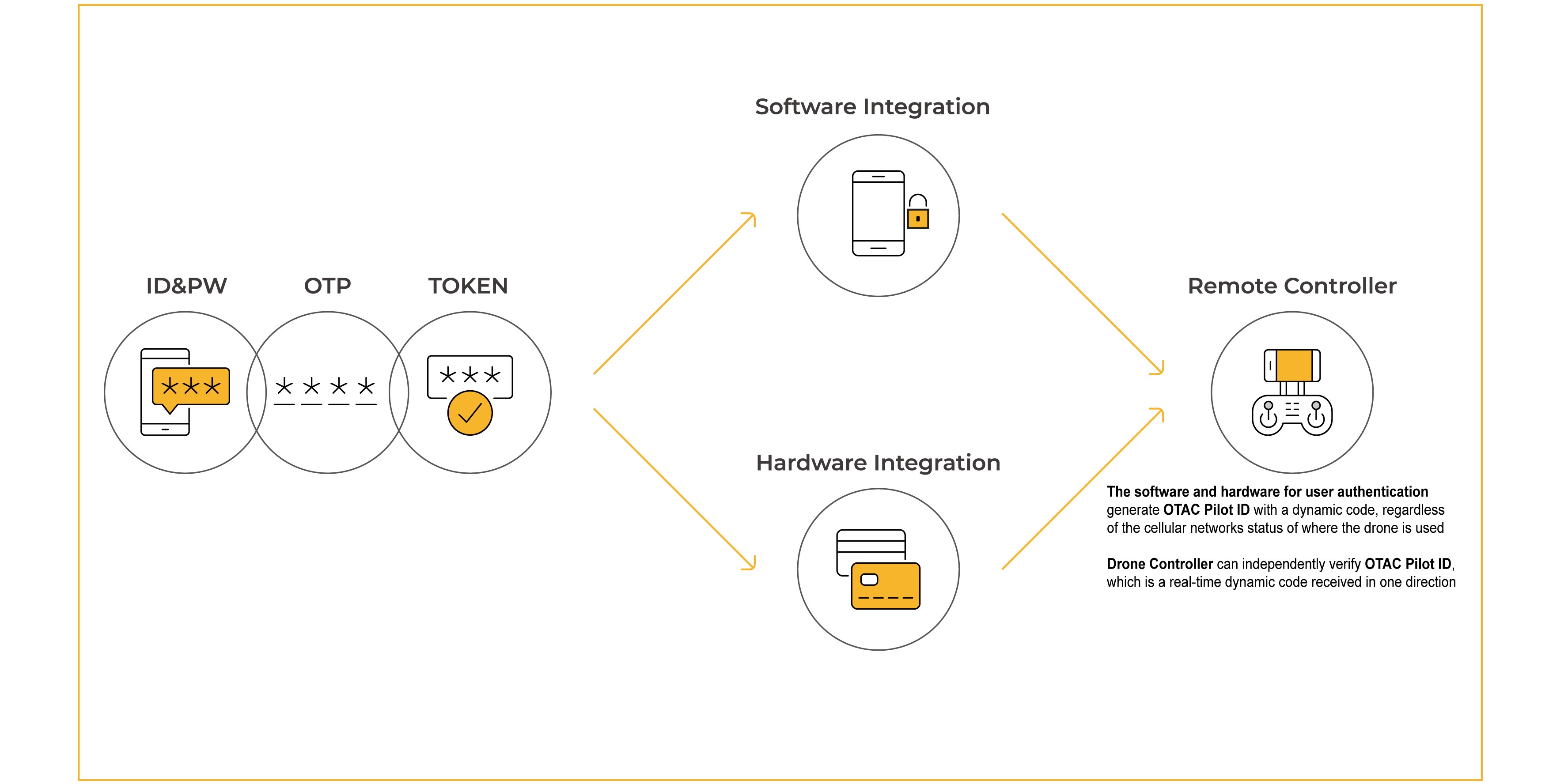
swIDch upgrades Drone solutions by preventing the use of static information and providing single-channelled dynamic codes to eliminate external threats. Our 'One-time-authentication-code' (OTAC) technology, which can be applied to both the software and hardware of the Drone, maintains and enhances the robust security environment level required for Drone manufacturers and system operators.
Access Management
OTAC Drone Command
Once the pilot securely accesses the control system via OTAC Pilot ID, the pilot can have full confidence in the security level of the command communication with the drone. Thanks to swIDch command, every single command generated from the remote controller will be in a ‘one-time, dynamic’ form. This means that every single command is unique, and even if a hacker obtains the command information, the command will be different next time round, preventing multiple forms of attack, including replay attacks, eliminating any risk of drone hijacking.
OTAC Pilot Access Management
OTAC Pilot ID
OTAC ensures that licensed pilots are provided with the highest level of security when accessing drone remote systems. Pilots can use swIDch's mobile app or display card to authenticate themselves and securely access drone control systems.
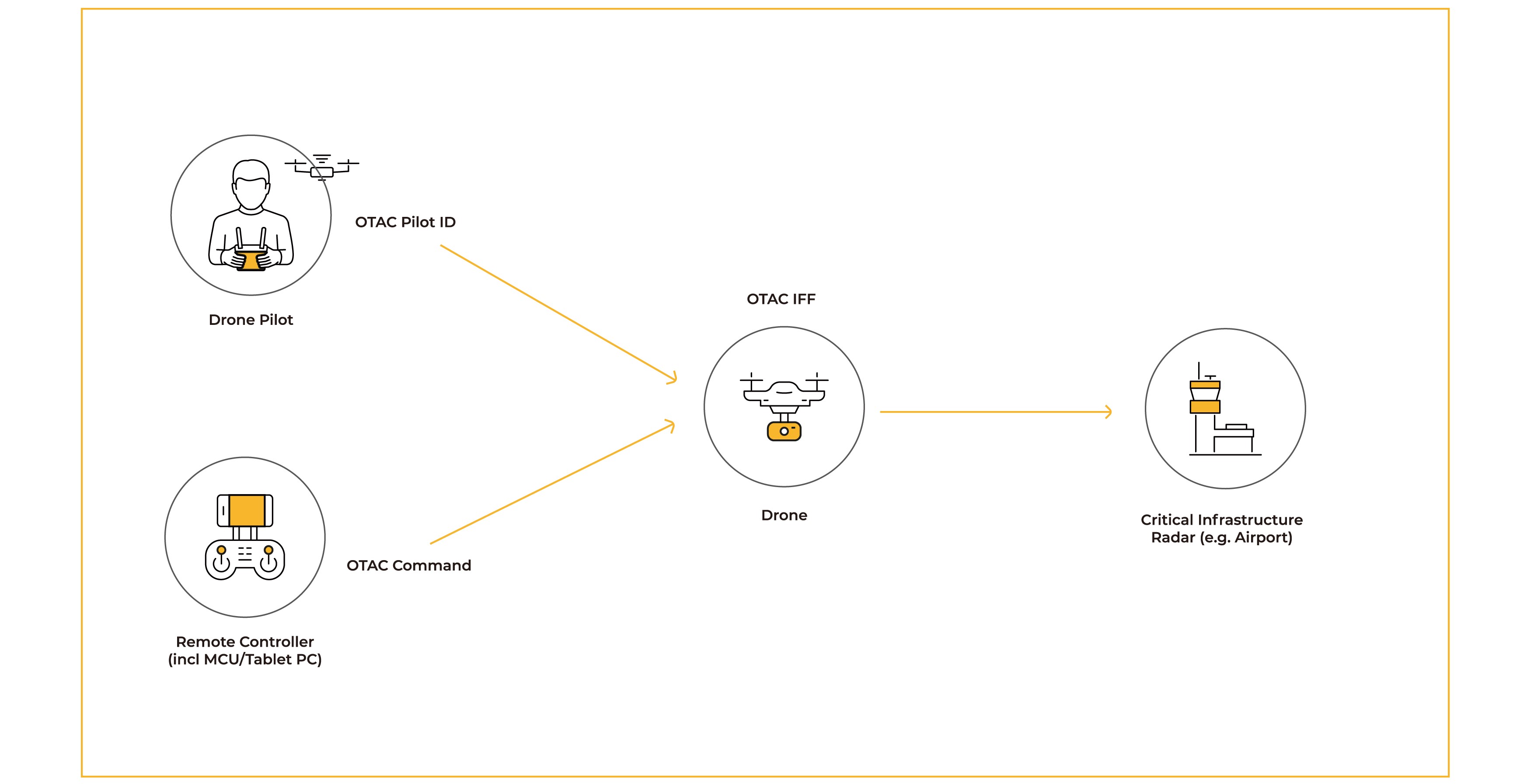
OTAC Pilot ID & IFF
OTAC converts all commands among the pilot, the controller and the drone into a one-time dynamic code to enable safe communication. If there is a security issue with the pilot, controller, or drone, you can immediately re-evaluate the status of the drone and register it as an enemy drone and take actions.
OTAC Drone Authentication
IFF (Identification of Friendly or Foe)
Identification friend or foe (IFF) is an identification system designed for command and control. It sends an encrypted signal to determine whether it is a friend or a foe by the return signal, but commands
can be stolen and misused. OTAC, a real-time dynamic ID code generated in the off-the-network environment, can identify friends whilst preventing theft and misuse of ID codes by the enemy.
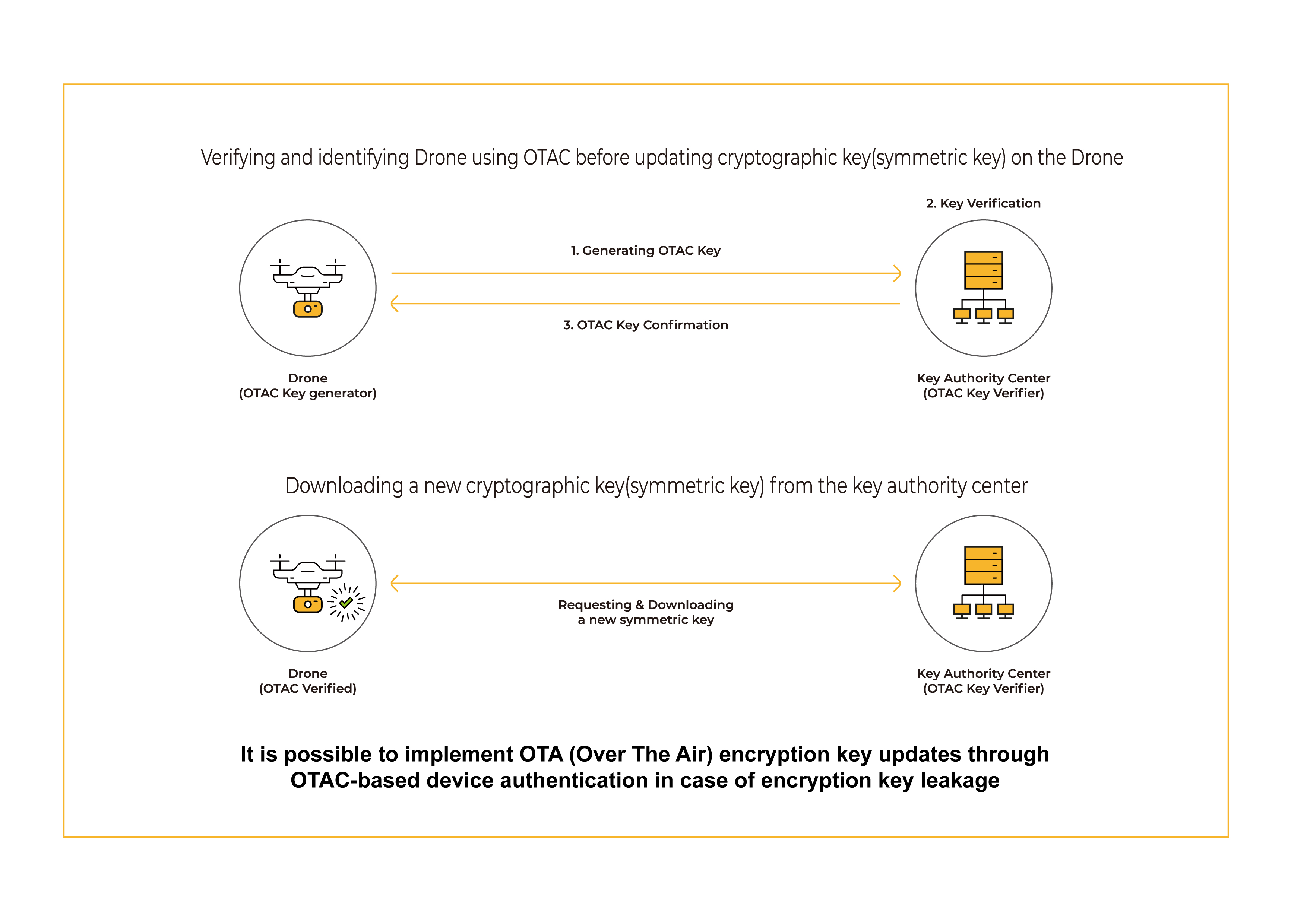
OTAC CMVP key management
OTAC can be used to protect communication encryption modules that have received CMVP certification and to authenticate key value updates. It provides an improved security environment by using dynamic codes for the identification and verification process of the drone accessed to download the new keys.
OTAC FDR
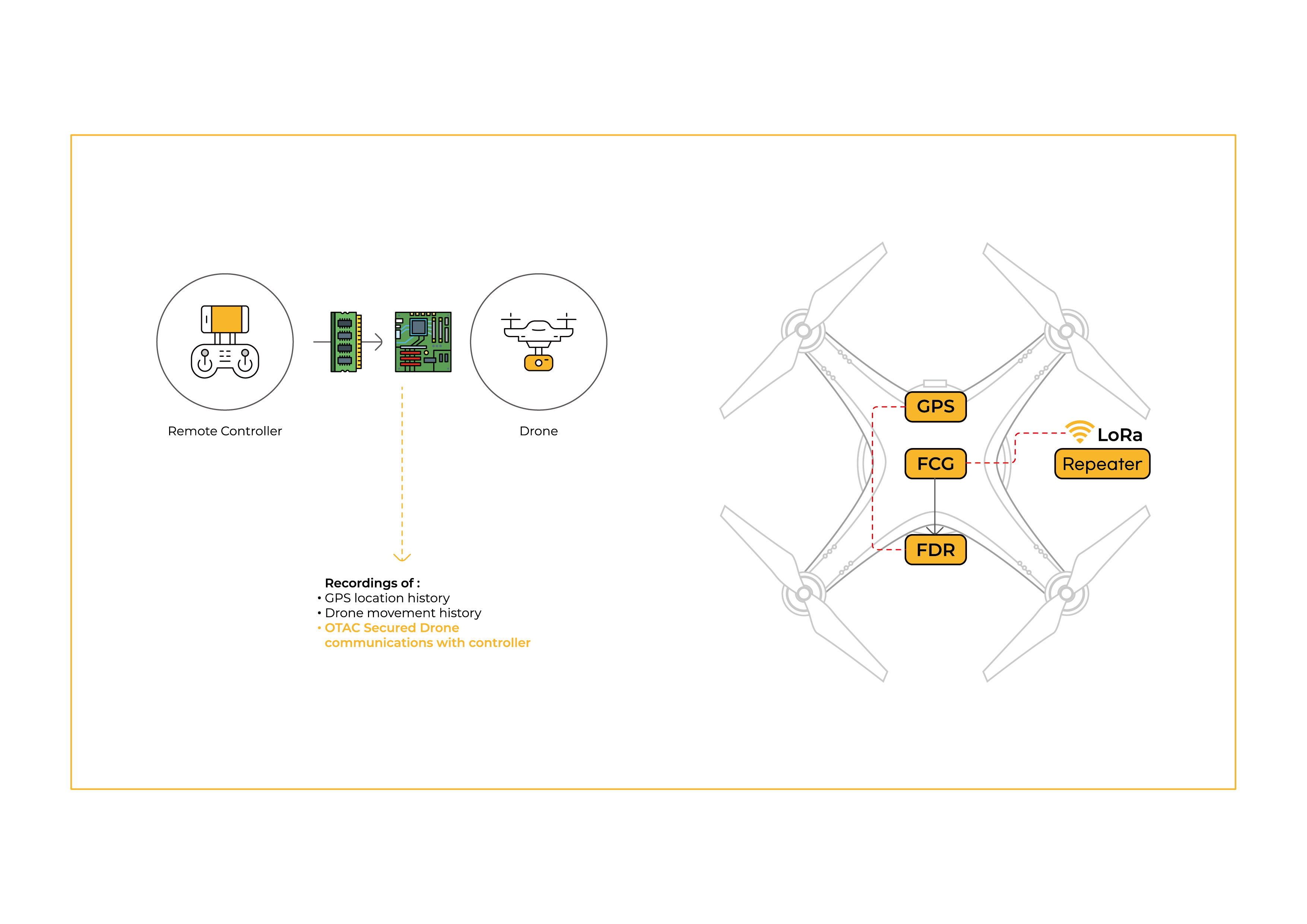
FDR (Flight Data Recorder) is a black box for drones; it monitors and tracks any events during the drone flight and missions. The tracking device has a very weak specification on forgery and alteration of data which further leads to use in wrong deeds. OTAC FDR is operated at the monitoring and tracking level on the system and generates dynamic codes to hide the sensitive data, thus enhancing the information security environment. Also, due to the nature of OTAC, the related data’s integrity is constantly evaluated to show if any data within the FDR is forged or altered in any way.
Why swIDch
that provides all of the following features, tested and substantiated
by the University of Surrey technical report
sufficient to IDENTIFY user
and AUTHENTICATION
off-the-network environment
Single-step identification and authentication with the code alone. Include our biometric option and get single-step MFA. Vastly improved UX by removing steps.
OTAC is a dynamic code, which means the code is constantly changing. Eliminates all use of static information. Forget usernames and passwords forever. Vastly reduced workload for IT helpdesks.
No network connection required for generating OTAC, enabling uninterrupted use no matter where you are. No more waiting for additional tokens/OTPs and no need for heavy public key infrastructure (PKI).
Highly configurable code parameters and lightweight SDK/applet means wide range of deployment options on many devices across multiple sectors.