The most enduring comfort in industrial...

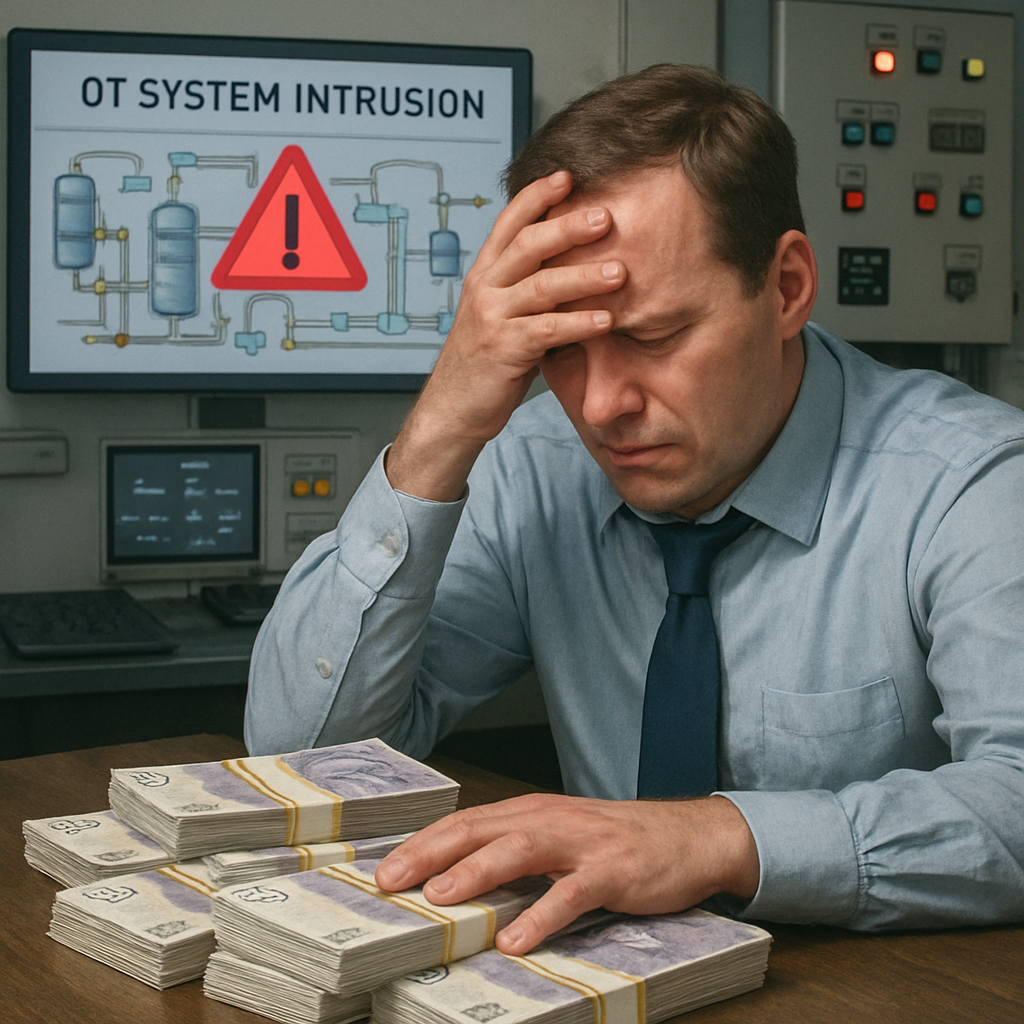
A startling figure has emerged from recent...

To destroy a single physical power plant in a...

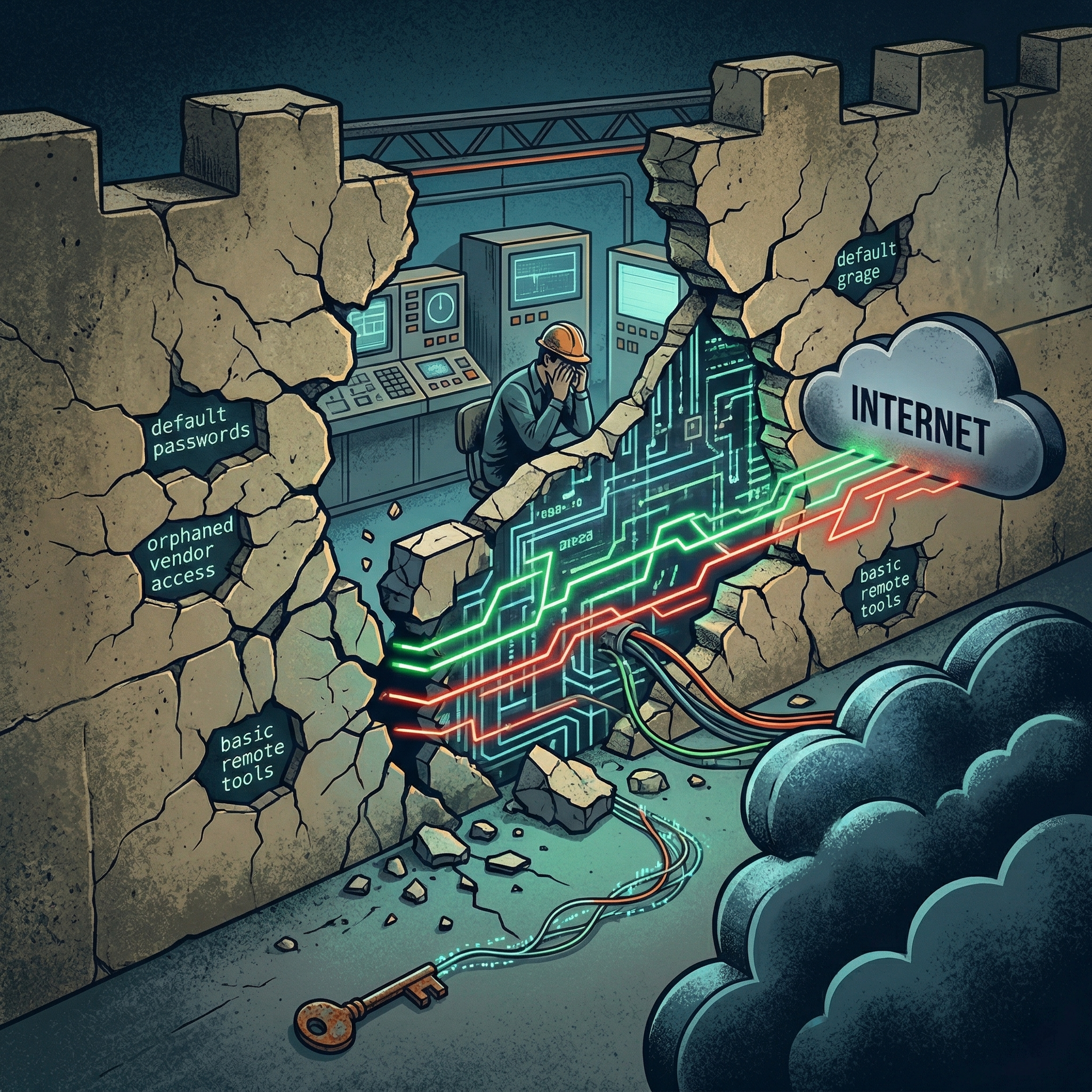
Across industrial sectors, most OT incidents do...

In late 2025,a coordinated cyberattack...

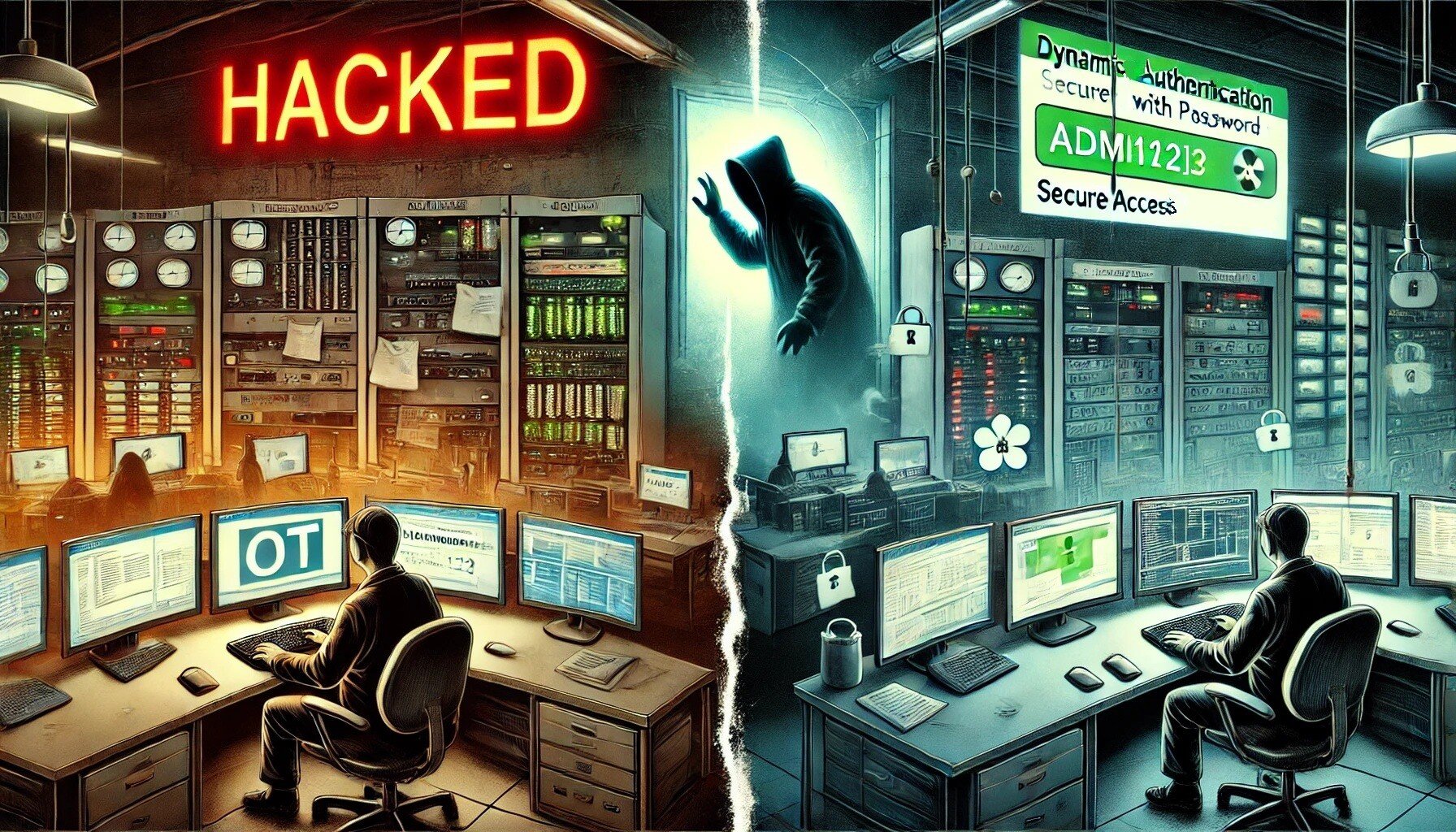
Approval has long been treated as a proxy for...

At a large industrial site, a contractor needed...

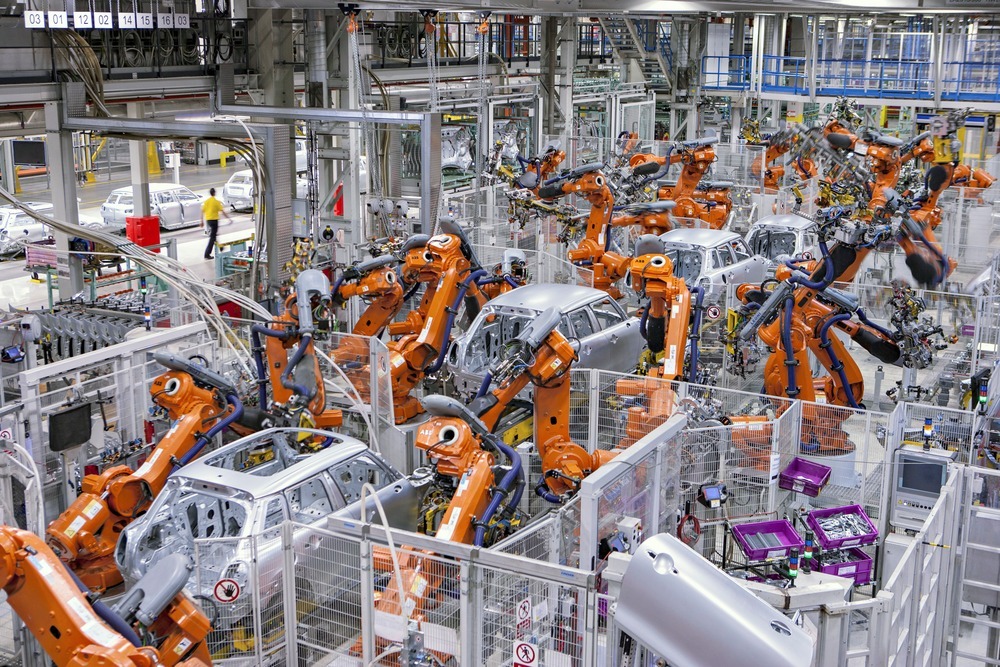
At a large manufacturing plant in Northern...

For many OT organisations, Passwordless still...

For years, Passwordless has been discussed as a...

Industrial operators step into 2026 with...

2025 made one truth uncomfortably clear: the...

The OT and critical infrastructure incidents we...

2025 was marked by a series of real-world OT...
Even after a year filled with operational...
Across industries, Operational Technology (OT)...

When a major U.S. steelmaker halted part of its...

In late October 2025, the Canadian Centre for...

A recent cyberattack on Jaguar Land Rover forced...
In October 2025, the European Union Agency for...

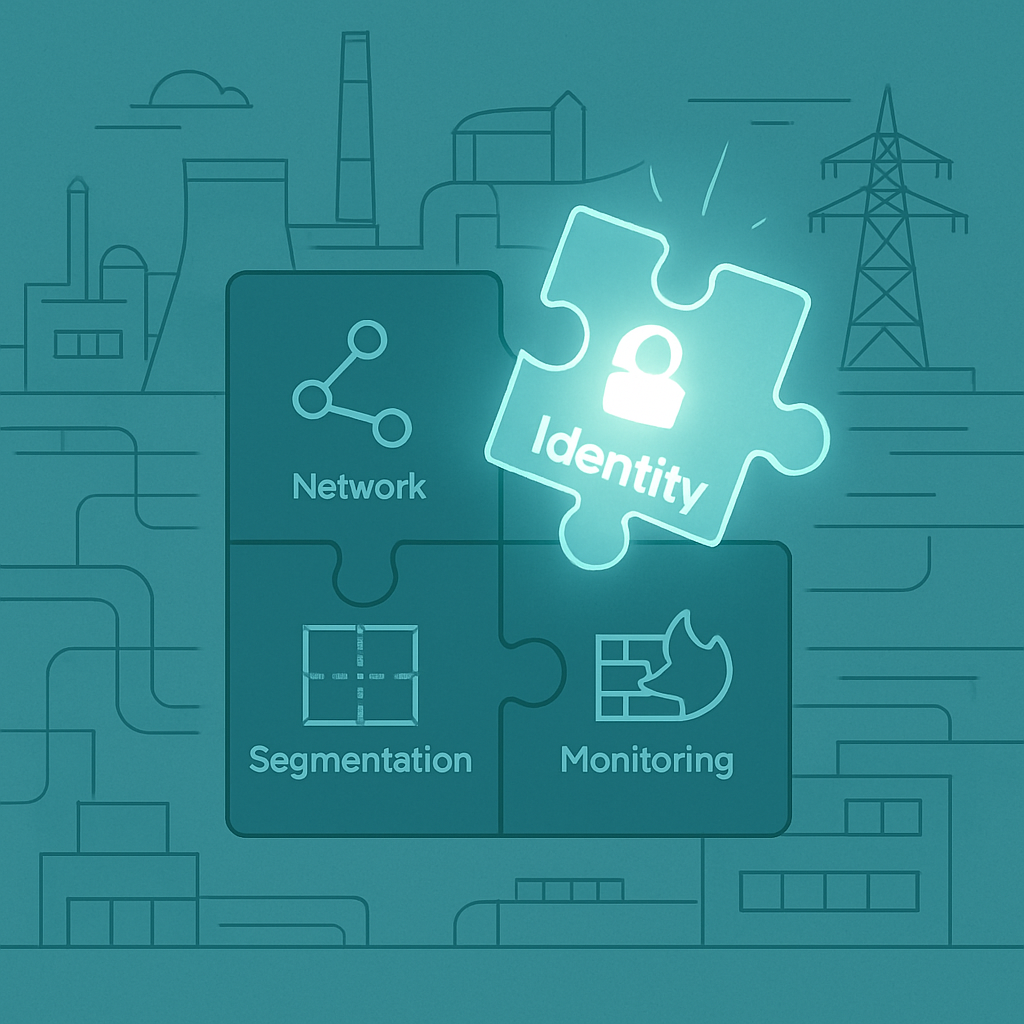
With 2026 approaching, many organisations are...

As organisations approach the end of 2025,...

Cyber security in operational technology (OT) has...

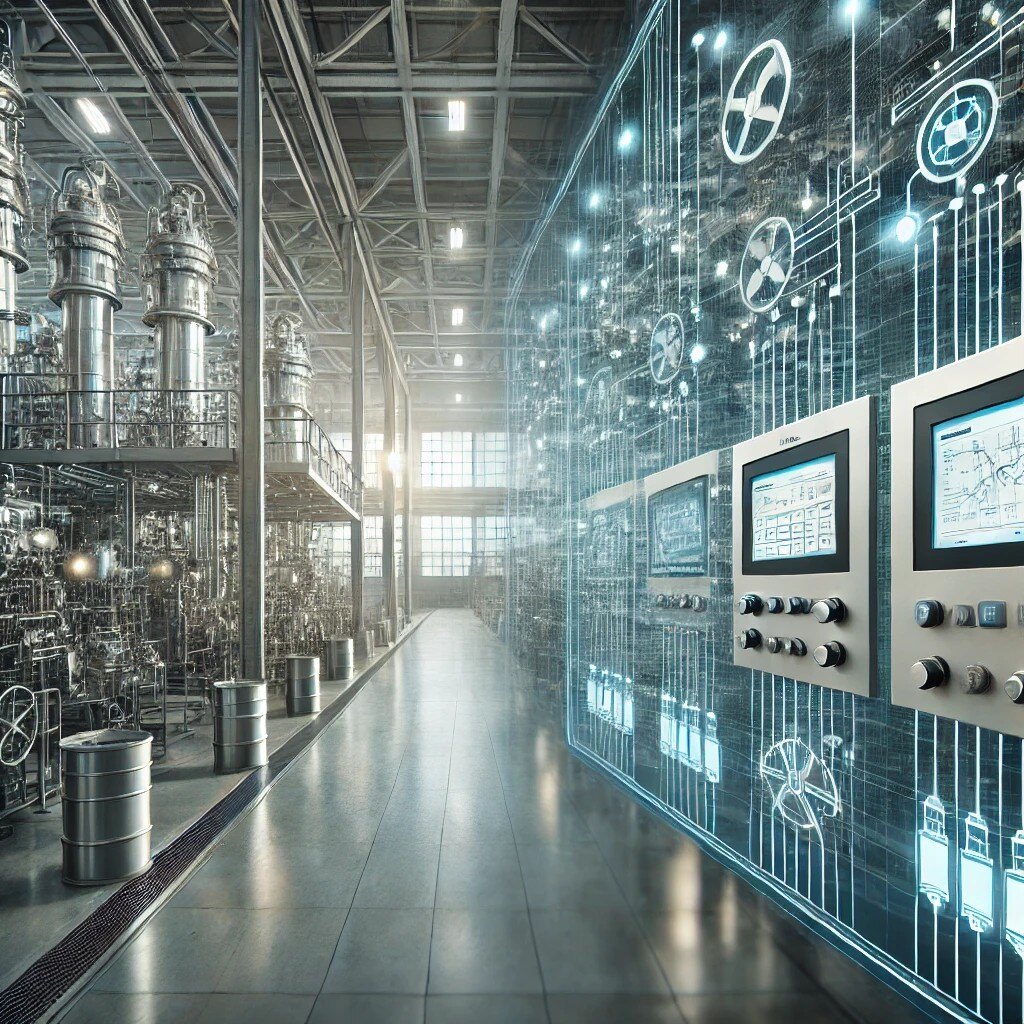
Industrial operations are rapidly moving towards...
This August, two independent studies made one...

In 2025, the UK government announced a bold...

The Cyber Resilience Act (CRA) is poised to...


Cyberattacks are everywhere in entertainment—from...

When it comes to OT (Operational Technology)...

The convergence of IT and OT systems has brought...

Operational Technology (OT) environments,...

Ransomware may start in IT, but it doesn’t always...

The NIS2 Directive is the EU-wide legislation on...

On a winter morning in 2024, several hospitals...
Operational Technology (OT) environments, which...
AI is no longer confined to massive central...

In late April 2025, Spain and Portugal were hit...

The distributed control system (DCS) is the...

In the age of digital transformation,...

The ubiquity of Public Key Infrastructure (PKI)...
When people think of cyberattacks, they often...
In the realm of Operational Technology (OT), the...

In the world of Operational Technology (OT),...

Cyber threats targeting Operational Technology...

In 2024, the realm of cybersecurity faced...
The world enters 2025 at the precipice of a...

In an era where technology integrates seamlessly...

Remote Terminal Units (RTUs) play a pivotal...
Historically, OT networks utilized proprietary...

Operational Technology (OT) devices, including...

In today's digital age, the importance of robust...

In the fast-evolving realm of operational...

There has been a noticeable rise in...

As industrial systems become increasingly...

In the ever-evolving landscape of cybersecurity,...
As artificial intelligence (AI) continues to...

In today's interconnected industrial landscape,...

When I transitioned from cybersecurity in IT to...

The maritime industry is undergoing a significant...

In the rapidly evolving landscape of Operational...

In an age where cyber threats are becoming...

In the realm of industrial operations, the...

In the digital age, where connectivity is...
.jpg)
In an era where digital frontiers are expanding...
In the dynamic landscape of cybersecurity,...
Quantum computers represent a paradigm shift in...

In recent headlines, an Israel-linked group has...
Artificial intelligence (AI) is pervasive in...

The online world is in constant flux, and so are...

The NIS2 Directive is the EU-wide legislation on...

In the realm of industrial automation, PLCs...

In a hyper connected world mobile phones have...

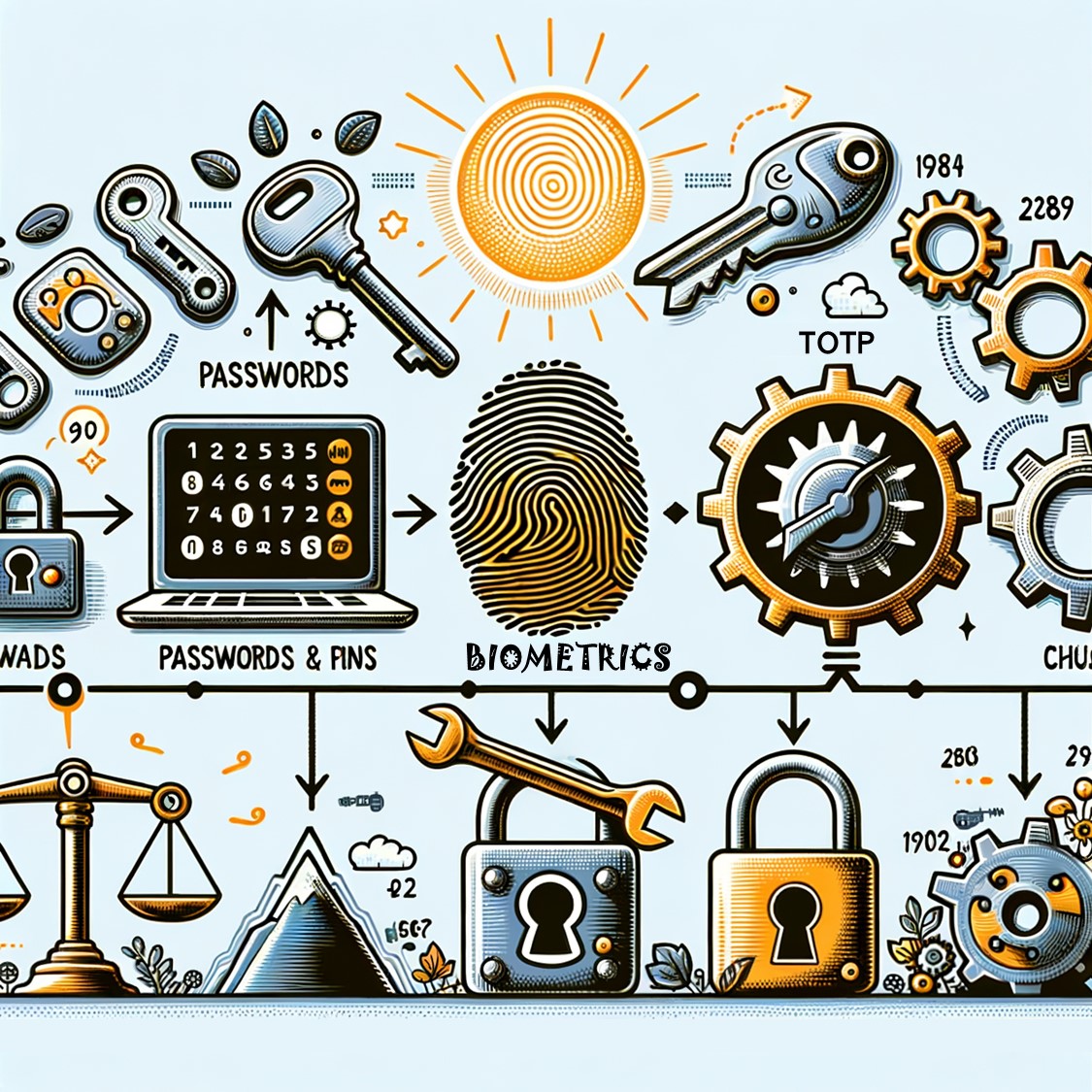
Many industries are changing their authentication...

Cyber security is a term that has become...
In today's interconnected world, the security of...

In an era marked by escalating cyber threats and...

In today's rapidly evolving technological...

Traditional perimeter-centric network security is...

2FA and MFA are methods of verifying a user’s...

In today's interconnected world, Operational...

The smart factory is a representative technology...

This is one of the most commonly asked questions...

In September 2022, 55 programmable logic...

While driving, sometimes a digital map guides you...

Throughout 2022, cyber security continued to...

COVID-19 has propelled society into a...
![Implementing MFA with swIDch's TAP-OTAC [Technical article]](https://www.swidch.com/hubfs/IT_twi001t3276159.jpg)
Abstract swIDch introduces an entirely new type...

In the film "Mission Impossible", Ethan Hunt, an...
.jpg)

Forbes notes the definition of a smart city to be...

If you transfer large sum remittance at once or...

swIDch is going GLOBAL. Meet swIDch LIVE at one...

The assumption that hackers take control of the...

For many 2022 has been highlighted as critical...

The quick and easy way we pay online is the most...
IoT provides opportunity for businesses to...

OTAC-embedded-Smart Card will change the future...

Governments are becoming increasingly aware of...

The world is getting smarter. As various products...

A recent report published by the Department for...

According to a study by Tech News World, more...

Welcome to the final instalment, part 4 of our...

Remote working environments are not necessarily...

Join me, Charlie Choi, for Part 3 of our Key IoT...

Join me, Charlie Choi, as I once again walk you...

The IoT (Internet of Things) accounts for the...

Back in 2010, the drone market exploded with the...

The potential benefits of drones to radically...

Social media hacking occurs day by day. The...
In today’s rapidly changing business environment,...

swIDch, an authentication technology startup in...
As social distancing has become common due to...

CyberTech is one of the fastest growing sectors...

The recent cyber-attack that paralyzed the...

Last year the Covid-19 pandemic saw a radical...

With the spread of cloud, remote work, and...
-1.jpg)
A smart factory that can enhance not only...
-1.jpg)
Smart cities are getting more attention over the...
-1.jpg)
The Internet of Things (IoT) beyond just...
-1.jpg)
The commercialization of connected cars became...
-1.jpg)
Digitalization extends to spaces ranging from...
-1.jpg)
The Web Summit, Europe's largest technology...

OTAC tech applied in Indonesian e-wallet App