Gen N Brings New Importance to User Authentication...

Remote working environments are not necessarily new to business, but are certainly fast becoming the norm with organisations forced to respond reactively and at speed to situations often without proper planning.
Add to this challenge the growth of Generation Novel (N), which categorises a cross-section of generations who prefer digital-first experiences, place greater value on personalisation and customisation, and demand transparency from the brands they buy from, work for and align to. The Gen N group focuses on technology more than others, whether it is at home or work... Read more here...
--------------------
swIDch Announces New, First-of-its-Kind Strategic Partnerships across Korea & Indonesia
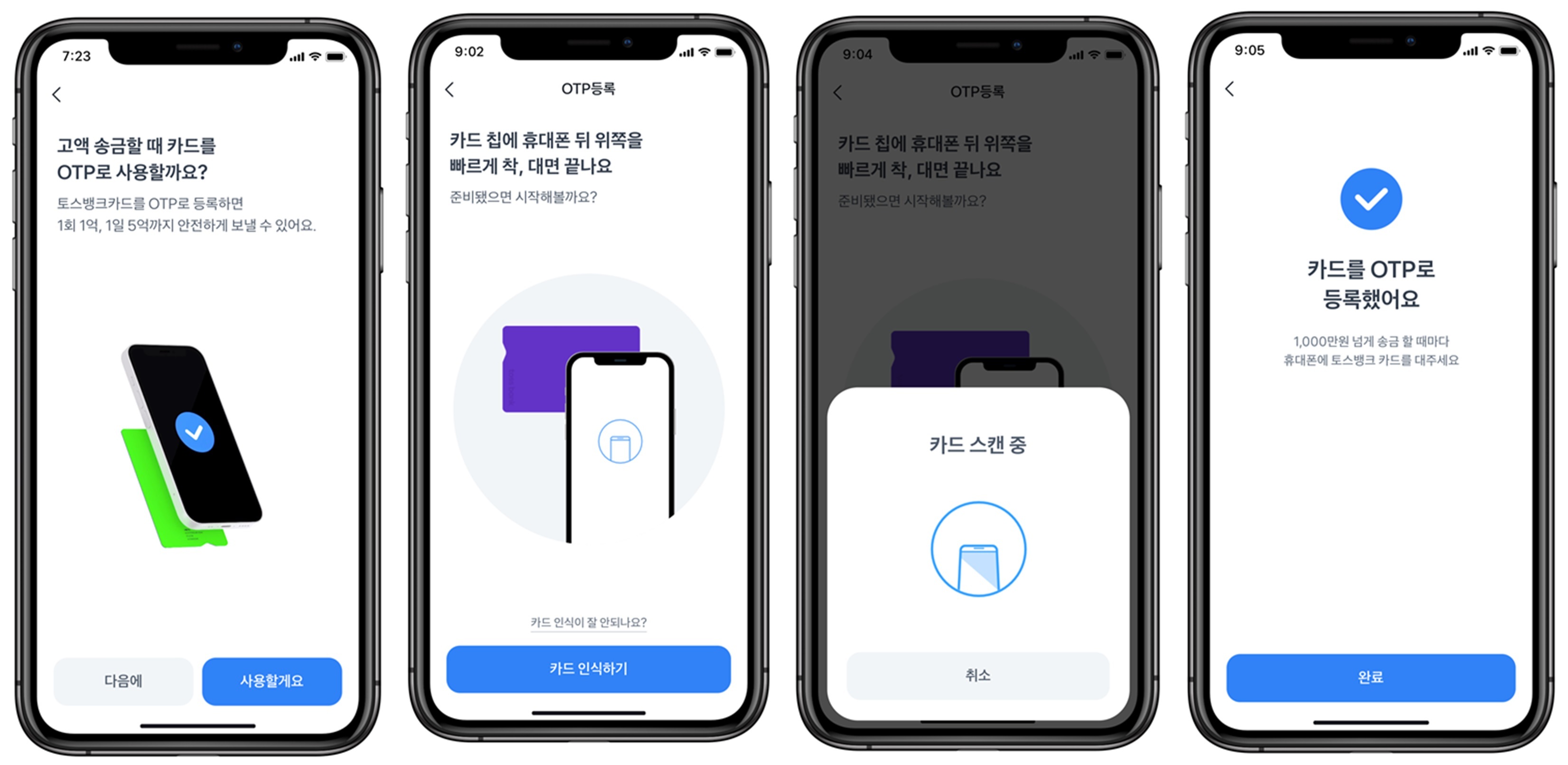
This month swIDch announced that it has been selected by Toss Bank, an internet-only bank, to supply switch OTP (one-time password), a card-tapping OTP generation technology, that can be used even on iPhone for the first time in Korea.
In addition to the Toss Bank partnership, swIDch also announced that it has partnered with PERURI, the Security Printing and Minting Corporation, in Indonesia to provide its unique OTAC technology as an authentication in line with the organisation’s overall digital transformation business.
Find out more 👉 HERE
--------------------
swIDch selected as part of UK Government funded Plexal Cyber Runway

swIDch has been selected to join this years Plexal Cyber Runway, funded by the The Department for Digital, Culture, Media and Sport (DCMS). Cyber Runway is the UK’s largest cyber accelerator, which is supporting 107 entrepreneurs, startups, SMEs and scaleups and we are very excited to be a part of this years cohort!
--------------------
swIDch shortlisted to win "Best Cyber Start up of the Year" at the Cyber Security Awards, 2021

The Cyber Security Awards reward excellence and innovation to the year's best individuals, teams, and companies within the cybersecurity industry. And we are once again in the running! Read more here... 👌
--------------------
Don't miss the final instalment [Part 4] of our "Key security vulnerabilities in IoT environment" technical blog series
The IoT (Internet of Things) accounts for the billions of physical devices that connect to the internet and provide remote control monitoring tasks. But what are the principal security vulnerabilities in IoT? And how do we effectively counteract them?
Take a deep technical dive with our technical director and a security advisor Charlie Choi as we dissect how hackers exploit these vulnerabilities. And how to be one step ahead of the game...
--------------------
Don't forget to follow us on our social channels to stay up-to-date with the latest updates from the team here at swIDch 👍

We'll be showcasing our next-generation authentication solutions at this years flagship cyber security event. We hope

swIDch launches 'Programmable Logic Controller OTAC' to revolutionise ICS & OT security Programmable logic controllers

Despite extremely volatile and turbulent economic conditions throughout 2022 and in particular towards the end of the
Looking to stay up-to-date with our latest news?