

Blog
insight and research in cybersecurity with swIDch Blog.
Popular
In the realm of Operational Technology (OT), the security measures applied to protect critical...

In the world of Operational Technology (OT), firmware updates are a necessary but often...

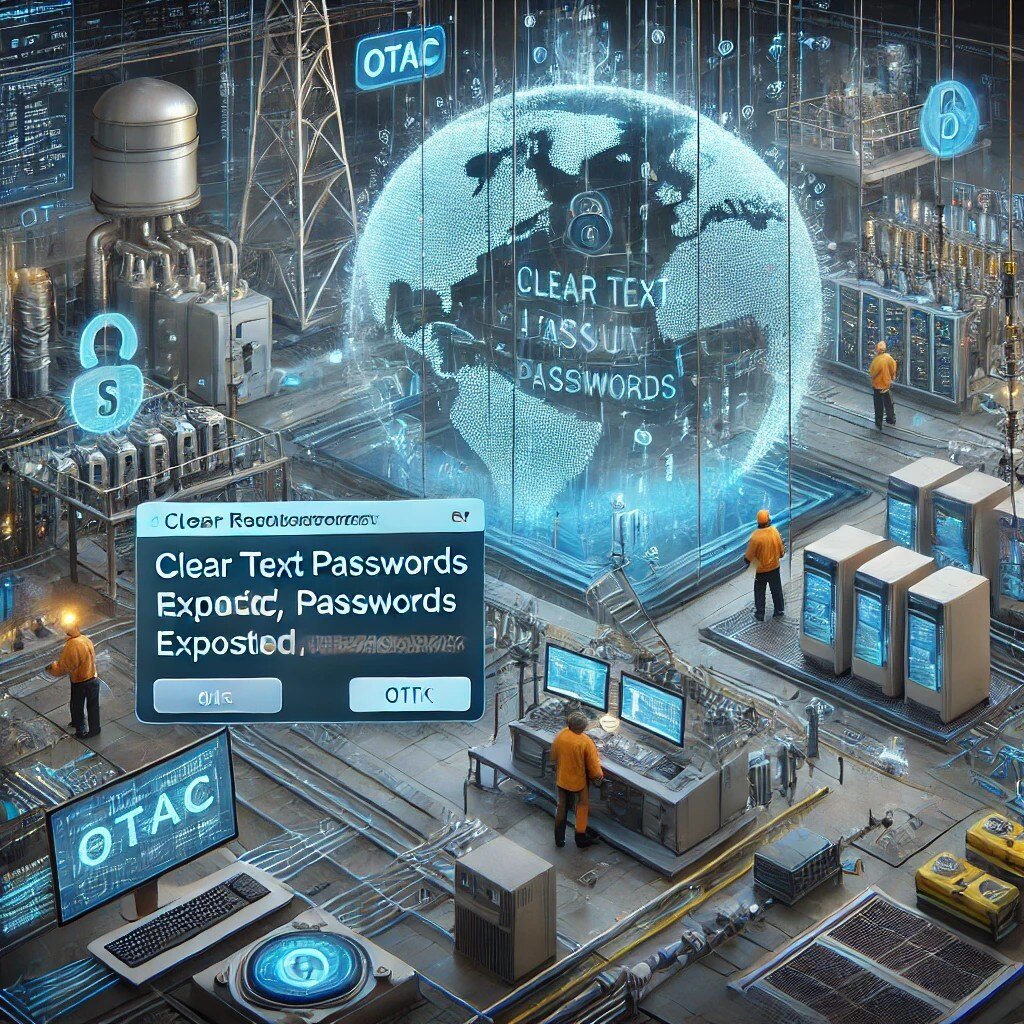
Cyber threats targeting Operational Technology (OT) systems have surged in recent years, placing...

In 2024, the realm of cybersecurity faced unprecedented challenges as the surge in Common...
The world enters 2025 at the precipice of a cyber age where the backbone of modern...

In an era where technology integrates seamlessly with operational processes, the importance of...

Remote Terminal Units (RTUs) play a pivotal role in industrial control systems (ICS), acting as...
Historically, OT networks utilized proprietary protocols optimized for specific functions. Some...

Operational Technology (OT) devices, including SCADA systems, Distributed Control Systems (DCS),...

In today's digital age, the importance of robust cybersecurity cannot be overstated. Yet, despite...
Looking to stay up-to-date with our latest news?
