Taking the leap - Overcoming security concerns to realise PLCs full potential

In September 2022, 55 programmable logic controllers (PLCs) used in major facilities in Israel were compromised by a hacktivist group called Ghost Security (aka GhostSec), highlighting the importance of PLC security, the workhorse of industrial automation. The reason why this incident received special attention is that many PLCs still use default login passwords, so hackers were able to easily infiltrate the industrial control system (ICS) and the supervisory control and data acquisition (SCADA) without using any advanced tech.
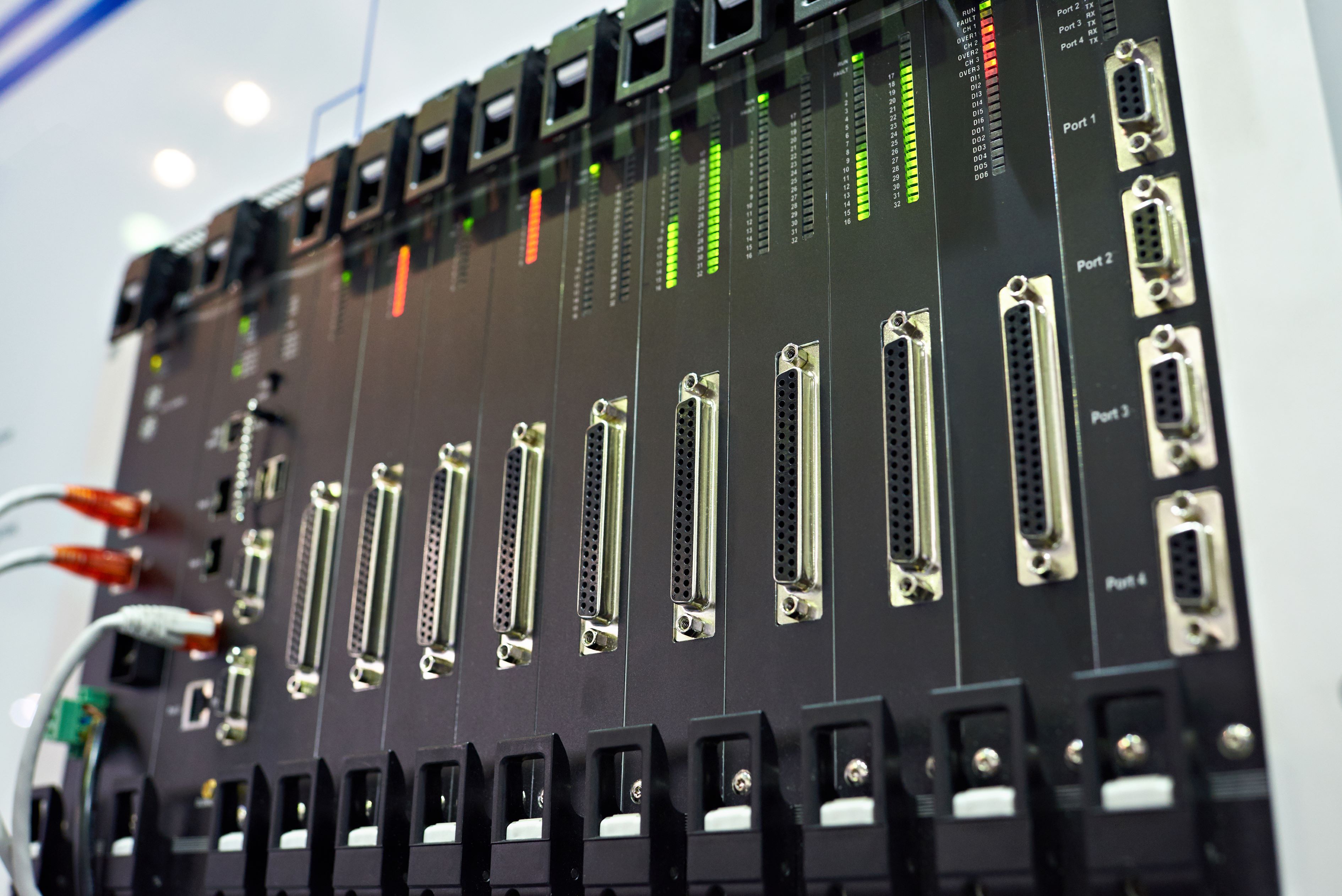
PLCs are at the heart of Industry 4.0. They are used as a simple machine automation control systems in elevators, road traffic signals, and automatic doors, and widely used in systems that operate, control, and improve machines in a wide range of industries including logistics, energy, and automobiles, as well as the automation of manufacturing processes in factory assembly. In the era of Industry 4.0, the key is to increase productivity by efficiently utilising the data produced by numerous industrial internet of things (IIoTs), so PLCs, which directly control machines, serve as a critically important gateway.
Global PLC market to reach $20.2 billion by 2028
The growth of smart sensors and industrial cloud markets is the driving force behind the PLC market. The global PLC market size reached US$ 14.6 billion in 2022. Looking forward, IMARC Group expects the market to reach US$ 20.2 billion by 2028, exhibiting a growth rate (CAGR) of 5.38% from 2023-2028.
However, as the number of PLC-applied industries and network-connected devices increases, problems are beginning to emerge. In addition to systemic problems such as module failure of the input/output (I/O) system, aforementioned frequency interference and power disruptions, security challenges due to the use of open networks for connection with numerous IIoT continue to grow. It is widely documented that many PLCs still use a user authentication process based on fixed values such as ID and PW, which makes it difficult to fully protect against human error or external threats, even if carefully managed by skilled engineers. This is why innovation of the user authentication process for PLCs access is desperately needed.
When a PLC is breached, the entire OT network is at risk
Claroty's hypothetical hacking test demonstrates that an entire operational technology (OT) network can be at risk if a hacker gains access to a PLC via remote access hacking. After compromising engineering workstations with the Evil PLC Attack which targeted the engineering software of the 7 leading ICS manufacturers, the attacker broke into the internal network and moved laterally between systems to gain additional access to other PLCs. As a result, it accessed every PLC on the network and manipulated the controller logic.
For a more secure PLC environment, it's possible to operate an internal network that is completely cut off from the outside or block wireless access altogether. However, many companies have a maintenance contract with the PLC manufacturer, so the PLC manufacturer's engineer often resolves issues remotely. This means that the closed network solution is becoming increasingly impractical. In addition, The 2019 GLOBAL ICS & IIoT risk report revealed that more than 84% of industrial networks already have one or more external devices that allow remote connectivity to internal industrial networks.
The next best option is to add multi factor authentication (MFA), which can verify users as authorized through already registered devices or bio information after going through the primary user authentication. The most common methods of MFA utilise biometric information such as fingerprints and irises, checking location information, or use one-time password (OTP). However, user convenience must be sacrificed to build such MFA. It is inconvenient to go through the 2nd and 3rd authentication after the primary authentication, and users must bring a designated device and there are restrictions on use in an environment where the network is unstable.
Why should you take note of OTAC for PLC access protection?
One technology that attracts attention as an alternative to MFA is one-time authentication code (OTAC). It provides strong authentication because it uses a one-time code that cannot be duplicated, and unlike MFA, it can be used directly as a primary authentication. Since it authenticates a user or device unidirectionally, the authentication process is almost instantaneous. As a communication network is not required when generating an authentication code, it can be employed even when the communication network is unstable or blocked.
Industry 4.0 is a demand of the times that can no longer be delayed. People who read paper magazines or write letters by hand will continue to exist in the future, but the majority of individuals, as well as organizations, businesses, societies, and countries, have already embraced a digital world with more connected devices. The more devices and people connect, the more actions and processes will be automated, and in this process, the role of PLCs will inevitably grow. A PLC free from external threats can play a pivotal role well beyond the status quo.
--------------------

swIDch will continue its quest to innovate and pioneer next-generation authentication solutions. To stay up-to-date with the latest trends sign up to our newsletter and check out our latest solutions.

In late 2025,a coordinated cyberattack disrupted parts of Poland’s power grid, affectingrenewable energy plants and

Approval has long been treated as a proxy for control. If access is approved, it is assumed to be safe. If the request

At a large industrial site, a contractor needed temporary access to a controller to complete routine maintenance. The
Looking to stay up-to-date with our latest news?