Who is responsible for the 5219 Rockwell PLCs exposed across the OT landscape

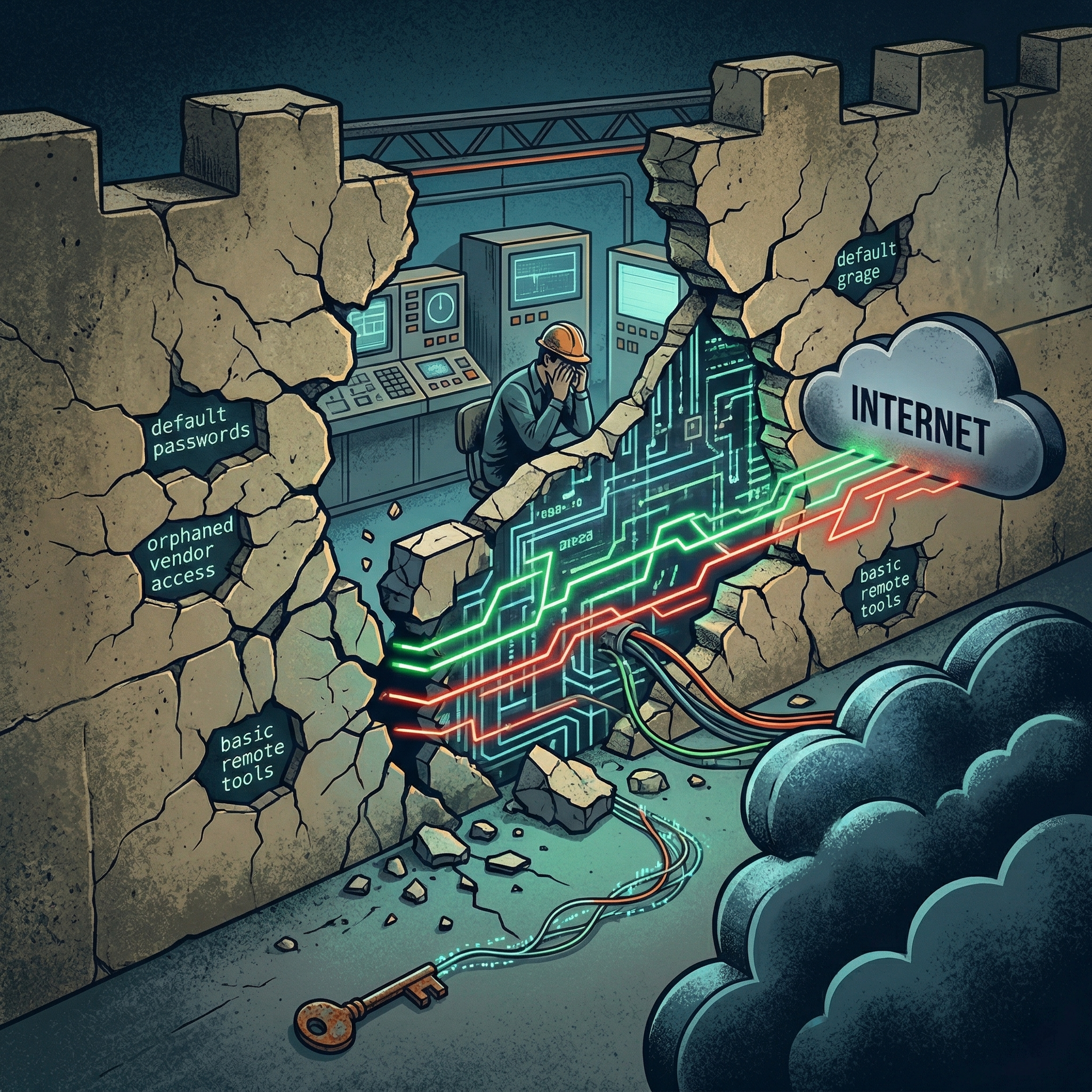
The recent Cybersecurity Advisory (AA26-097A) issued by the US Cybersecurity and Infrastructure Security Agency (CISA) has exposed a raw and uncomfortable truth about the current state of Operational Technology (OT) security. When Iranian-linked actors compromised US water facilities, their weapon of choice was not a sophisticated piece of custom malware. Instead, they simply walked through the front door using the manufacturer’s 'default credentials' to access engineering software.
The figure we must confront is 5,219. According to a 2026 analysis by Censys, this is the number of Rockwell Automation PLCs currently exposed directly to the public internet. This is not a slight against Rockwell’s engineering; on the contrary, it is a paradoxical testament to their status as a global industry standard. Because these devices are the most trusted and widely utilised, they have become the most significant battleground for adversaries. The real issue lies in the fact that, from the moment of installation, many of these devices have remained operational without the most fundamental layer of security: robust identity authentication.
The Era of Malware-Free Attacks

We are now facing a tactical shift known as ‘Living off the Land’ (LOTL). Rather than exploiting software vulnerabilities, hackers are leveraging the very tools engineers use daily—such as Studio 5000 Logix Designer—to gain control. To the system, there is no discernible difference between a legitimate engineer and a malicious actor because there is no 'digital identity card' to distinguish them. Once inside, the adversary possesses the same level of authority as the plant manager.
Engineers on the ground are acutely aware of this risk. However, a formidable technical barrier has historically stood in the way of a solution. In OT environments where connectivity is often intermittent and legacy hardware may be decades old, implementing IT-style Multi-Factor Authentication (MFA)—which requires constant communication with a central server—is frequently a physical impossibility. The fear that an authentication server failure or a latency spike could trigger a catastrophic process downtime has forced a compromise: choosing availability over security. Consequently, operators have been left with little choice but to fortify the perimeter while leaving the internal 'gates' wide open.
The Necessity of Authentication at the Edge

For too long, the industry has fixated on 'detecting' intrusions at the network boundary. Yet, as LOTL tactics demonstrate, an intruder using legitimate tools can bypass even the most expensive monitoring solutions. The question must shift from "How do we find the intruder?" to "How do we prove the identity at the device level?"
To solve this without compromising the availability of global PLC hardware, we require an approach that departs entirely from traditional, communication-reliant authentication. Security must be decentralised; the device itself must be capable of validating a trusted token without needing to 'call home' to a server. This logic must be lightweight enough to avoid interfering with critical processes, yet robust enough to meet international standards such as IEC 62443. This is why critical national infrastructure and global manufacturing sites are increasingly turning towards 'Non-communicative Dynamic Authentication'. By generating non-reusable, time-synchronised codes at the edge, it is now possible to secure legacy assets from vendors like Rockwell or Siemens without modifying the underlying logic or risking downtime.
A Call for Sustainable OT Governance

As offensive tactics evolve, our defensive posture must undergo a fundamental shift. Simple password rotations are no longer a viable defence against the current generation of LOTL threats. When manufacturers and operators move beyond legacy mindsets to consider architectures like OTAC (One-Time Authentication Code), our infrastructure will finally begin to outpace these persistent threats.
Security should not be a hindrance to industrial efficiency; rather, it should be the foundation that makes long-term productivity possible. It is time to move away from performative security policies and embrace technical alternatives that actually work in the unique, unforgiving environment of the plant floor.
--------------------

swIDch will continue its quest to innovate and pioneer next-generation authentication solutions. To stay up-to-date with the latest trends sign up to our newsletter and check out our latest solutions.

As industrial organisations enter the second quarter of 2026 a fundamental shift in the cyber insurance market has
The most enduring comfort in industrial security has always been the concept of physical isolation. For decades plant

A startling figure has emerged from recent global OT security research that should keep every plant manager awake at
Looking to stay up-to-date with our latest news?