Top 3 IoT Security Trends for 2022
For many 2022 has been highlighted as critical in terms of IoT security, with The PSA Certified 2022 Security Report labelling 2022 as the ‘turning point’ year signalling a paradigm shift in the way companies approach the topic. In the report, 88% of respondents agreed security was a top three business priority, 96% viewed security as positively impacting their bottom line, with 68% of respondents agreeing trusted components built on the Root of Trust are vital to unlocking security at scale. So, what are some key IoT Security trends for 2022? And how will they impact the upcoming year?
Continued Impact of COVID-19 on the IoT Security Market
The COVID-19 pandemic had a significant impact on the IoT security market. The knock-on effect of border closures and strict lockdowns meant that many manufacturers were forced to close which in turn heavily impacted supply chains resulting in structural shifts that had significant implicants on this industry globally. Secure communication, unified threat management, and IAM automated systems helped by automated IoT security features helped many manufacturers keep going during the pandemic. However, for many businesses IoT security took a backseat whilst they attempted to keep things going and adjust to the seismic shifts in global markets and deal with market uncertainty. This also left many businesses unprepared from a security perspective as restrictions were lifted and demand increased rapidly over a short period of time.
Nonetheless, COVID-19 also led to a refocus of IoT security in some sectors, none more so than that of the healthcare industry. As the pandemic grew, the direct strain on healthcare networks and systems which includes life saving operations and reliance on critical medical devices became apparent. ‘Telemedicine’ and remote working for healthcare professionals became commonplace which resulted in a need for swift action in terms of remote working security systems. In addition, Vigilance became an even greater priority which saw an explosion in adoption of IoT security technology to control fraud related to health devices and patient data. What is clear is that the repercussions from this seismic event will continue well into 2022.
IoT and PKI
Recently there has been an explosion of IoT devices, especially in relation to smart city, smart energy, and even smart home device infrastructure. Ericsson predicts that this year we will have around 29 billion connected devices globally, of which around 18 billion will be related to specifically to IoT. What is happening on a more technical level is that security technology in general is moving away from pre-shared key management towards a public key infrastructure. This shift brings with it the potential for a vast array of new solutions. These include Zero Trust, Post Quantum as well as IoT and access management.

A PKI is an IT foundational building block. It includes hardware, software, policies, processes, and procedures to manage digital identities. PKIs are not a new phenomenon. They have been used for decades to verify the identity of enterprise users and devices, and to authenticate them across different types of networks. Without reliable, secure PKIs, online transactions and communication would have no security framework. PKIs issue digital certificates to securely identify and authenticate individuals and servers online. These certificates must then be signed by a trusted Certificate Authority or CA. The private keys used for this purpose underlie the security of the whole PKI ecosystem. PKI thus is critical to the Internet of Things (IoT) and so too is the integration of a Hardware Security Module (HSM) when deploying a PKI. HSMs form a vital component of the PKI as they provide the root of trust needed to securely store and manage these critical singing keys.
Connected devices now outnumber users due to the rapid expansion of the IoT industry. As a result, PKIs and digital certificates have become even more important. When IoT devices are initially manufactured, each one is assigned an identity, which is essentially a digital birth certificate. This means the device can be identified and authenticated throughout its lifecycle. With more interconnected devices coming online, PKIs are being expanded to meet the demands of the IoT. PKIs must provide production control to ensure authenticity of devices, injected certificates to certify device identity and code signing to substantiate the integrity of their software. In addition, the data collected from these devices is highly valuable, but if businesses cannot trust the data collected it becomes meaningless. Therefore, the root of trust using certified high assurance HSMs to hold and manage critical signing keys is of utmost importance.
Edge computing & Edge IoT
Edge computing basically means that most of the computing take place on the device where the data is collected. The data is thus processed very close to or directly on the physical product, for example on wearable devices, smart phones, smart cameras, and smart machines. At the other end of this network structure is the cloud. Data can also be sent from the product via the internet to the cloud and only processed there, in contrast to edge computing. However, in most instances edge computing, edge IoT and the cloud go hand in hand with more of the processing being divided between the edge and the cloud.
Typical edge computing tasks can range from simple average value calculations like mean temperature from the device to complex pattern recognition with neural networks. If neural networks are used, this is often referred to as edge A.I. According to IBM ‘neural networks, also known as artificial neural networks (ANNs) or simulated neural networks (SNNs), are a subset of machine learning and are at the heart of deep learning algorithms. Their name and structure are inspired by the human brain, mimicking the way that biological neurons signal to one another.’ However, this subset of edge computing requires a separate article to address in detail but nonetheless it is worth mentioning as it may become a more widely used term as we move into 2022.

So, what are the key benefits in processing the data directly on the device? The first is local availability. Many IoT products must function without connection to the internet. This means the necessary processing must be done on the device itself without overreliance on networks. Second is in relation to data privacy. Often information is pre-processed on the device for privacy reasons. A good example of this is the recognition of license plates for entry into underground garages. Only the number values of the plate are stored as opposed to the image of the complete car and driver to verify entry which would require information sharing between the device and server/cloud. The driver identity remains secure whilst the information stored on the entry device is enough to verify the driver. The final benefit is in relation to energy and data volume. Many IoT products are battery driven with most of this energy being used during the transmission of information to the cloud. The better the information is pre-processed on the device; the less information needs to be transmitted. This saves energy and data volume costs which is particularly important for many devices. In the case of SIM card authentication for example, the majority of the processes required for authentication and verification happen within the device itself either via a removable or embedded SIM (eSIM as used in smart factories), with energy and cost saving benefits coupled with increased security, a win win for end users and businesses.

In 2026 downtime in the industrial sector is no longer viewed as a mere operational hurdle but as a direct haemorrhage
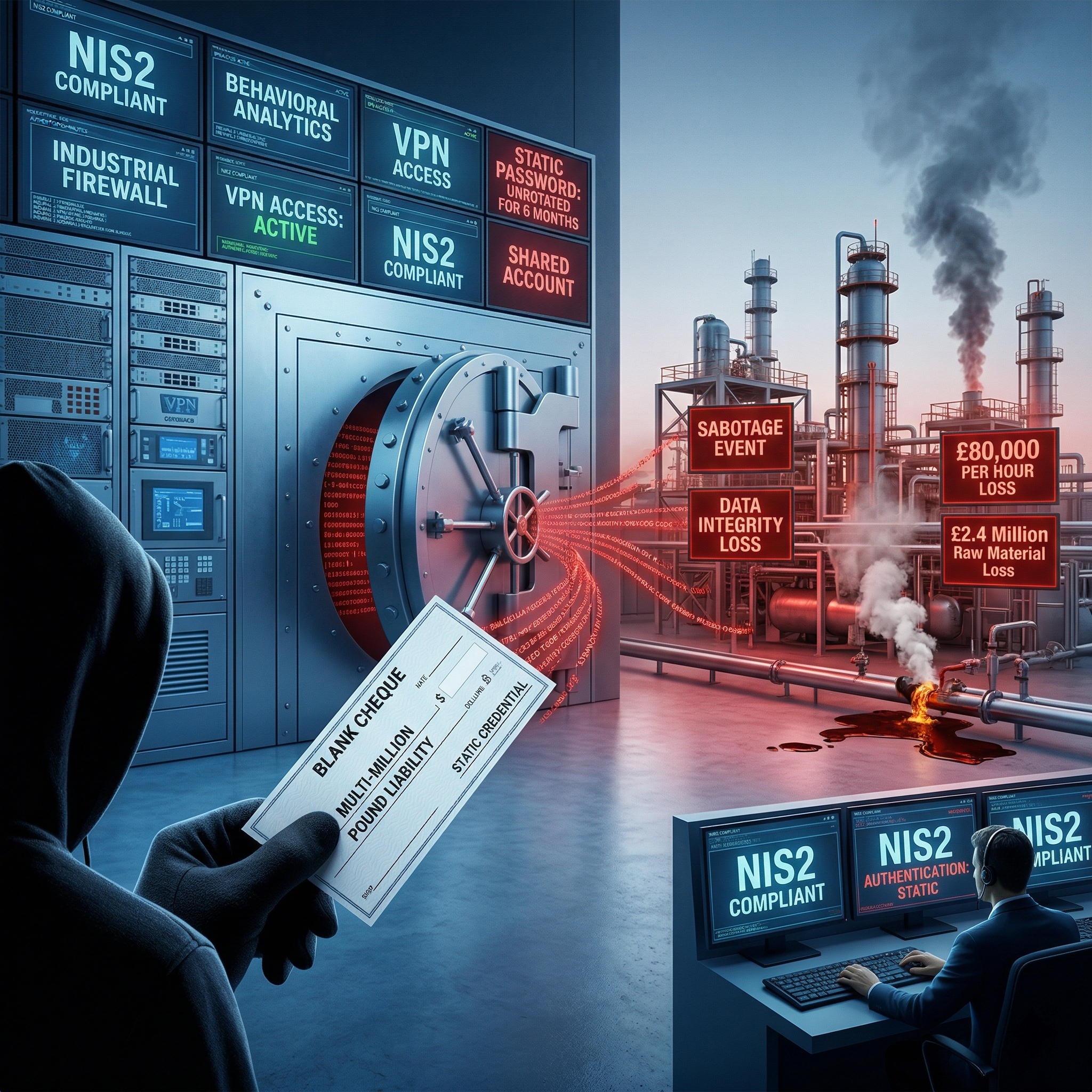
In 2026 the reliance on static passwords within Operational Technology is no longer just a technical vulnerability but
Anthropic's Claude Mythos marks a definitive shift in the cybersecurity landscape. We are no longer discussing AI as a
Looking to stay up-to-date with our latest news?
