A compromised access point can stop operations, damage equipment, or impact safety.
That’s why OT security must start at the endpoint — not the network.
OTAC Trusted Access Gateway (TAG) enforces authentication before access reaches your PLCs, without changing existing infrastructure.
Strong authentication — without operational disruption
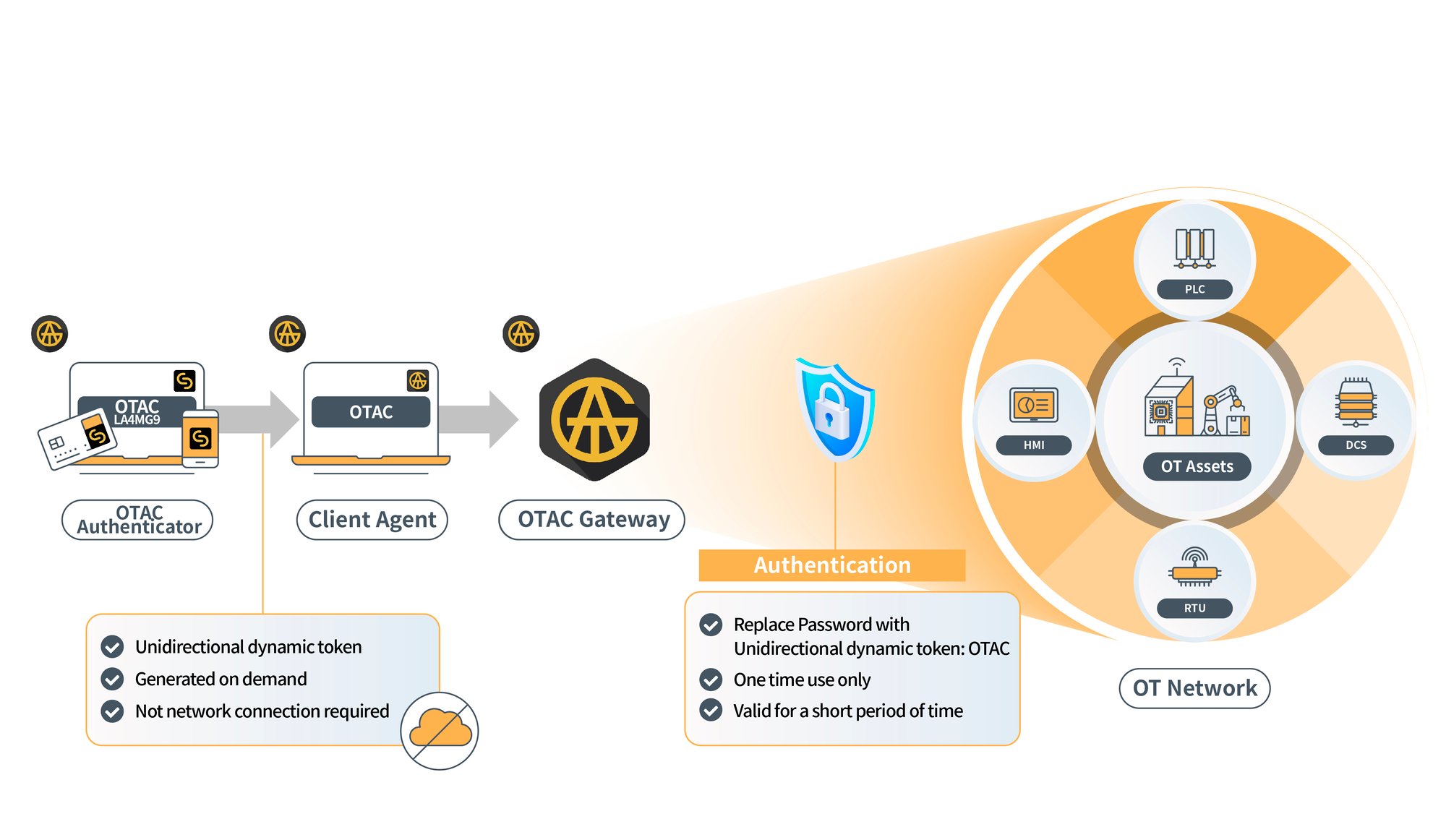
One-time authentication codes (OTAC) generated from registered user devices:
- No Static Credentials: Minimises data breach risks by eliminating stored sensitive data.
- No Network Dependency: Operates via one-way authentication without an active connection.
- Air-Gapped Ready: Optimised for critical infrastructure and isolated environments.
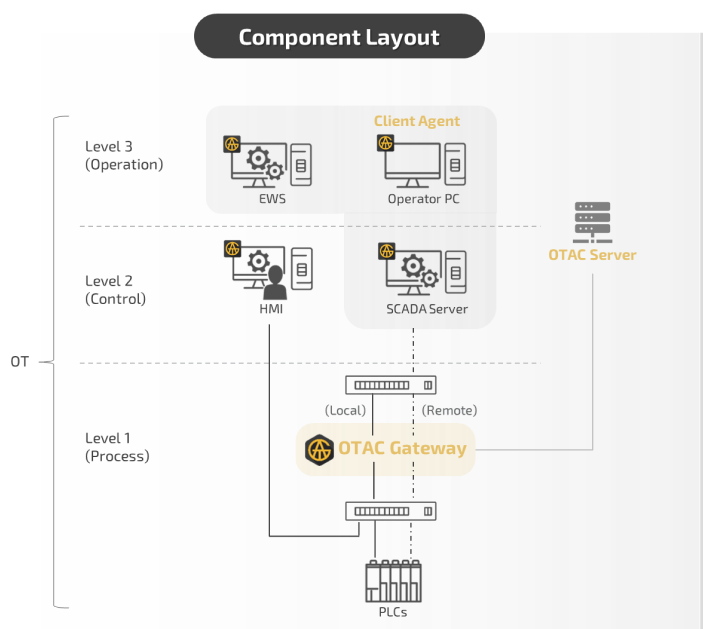
The following components work together to enable secure, endpoint-level authentication across OT environments.
- OTAC Authenticator generates OTAC via a mobile app or dedicated hardware devices, such as smart cards
- Client Agent triggers authentication when users attempt to access the system via engineering software
- OTAC Gateway enforces access control at the point of access to OT systems
- OTAC Server validates authentication and manages access policies.
- Admin Portal provides centralised management of users, policies, and access logs.
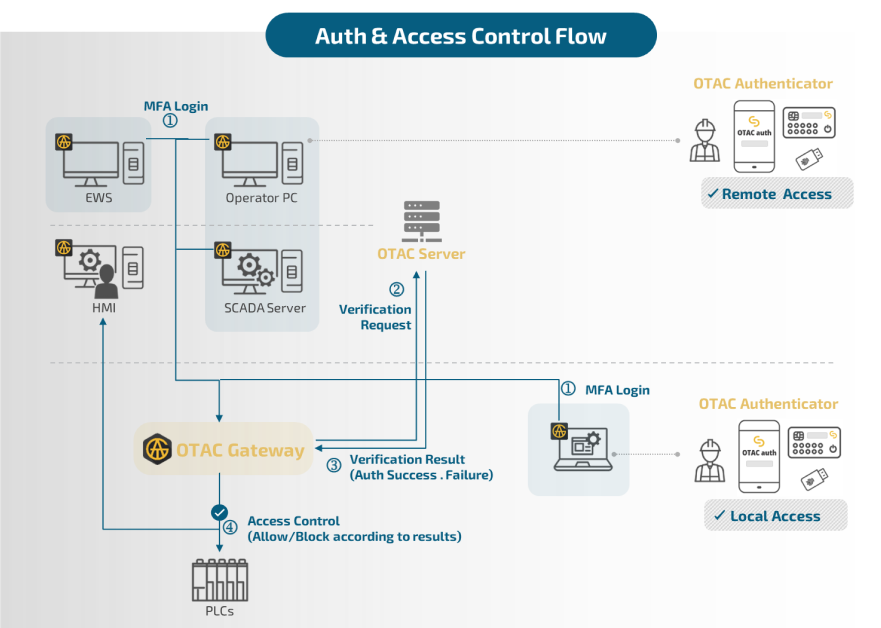
How It Works
The OTAC Trusted Access Gateway integrates seamlessly into your existing infrastructure. Here is a simple breakdown of the process:
- Deployment: The Gateway is positioned between the access device (PC/Laptop) and the target OT system.
- Request: Launching an engineering application (PLC/HMI/RTU/DCS) triggers an authentication request via the Client Agent.
- Generation: The user generates a dynamic OTAC on their registered device (smartphone or smart card) and enters it for verification.
- Validation: The Gateway validates the code and grants access only to authorised users, securing the system at the gateway layer.
This ensures all access is verified before commands reach the endpoint, adding a critical layer of protection for physical control devices.
Key Benefits
The OTAC Trusted Access Gateway provides a seamless upgrade to OT authentication environments without complex system modifications.
- No Need to Replace Legacy PLCs: The PLC devices remain intact, with no vendor firmware changes required.
- Endpoint-Level Security: Secure access is enforced at the device interface, allowing precise control over who can interact with critical OT components such as PLCs, HMIs and RTUs.
- Centralised Management: User authentication can be centrally managed for enhanced control.
- One-Way Dynamic Authentication Codes: Static passwords are replaced with dynamic codes that change for each session, ensuring secure user and device authentication.
- Comprehensive Access Logs: Unlike standard PLC access logs that lack user/device identification, OTAC Trusted Access Gateway’s logs provide meaningful, actionable records of access activity.
Case Studies
Global energy solutions manufacturer
Enhancing PLC asset protection through endpoint authentication, preventing unauthorised access
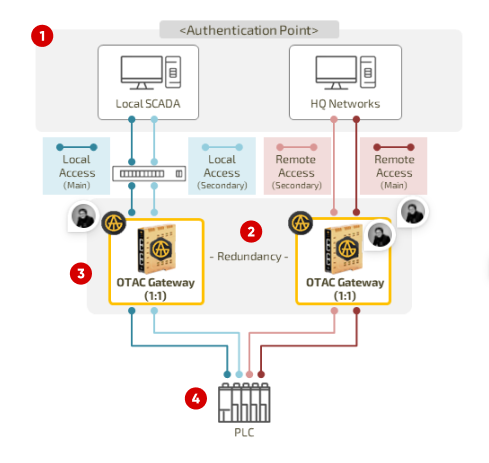
① Designed to support both local and remote access via the OTAC Gateway at each authentication point.
② Applies a blacklist policy — Requires user authentication for endpoint devices registered in the admin portal.
③ Controls user access to each endpoint device via OTAC Gateway.
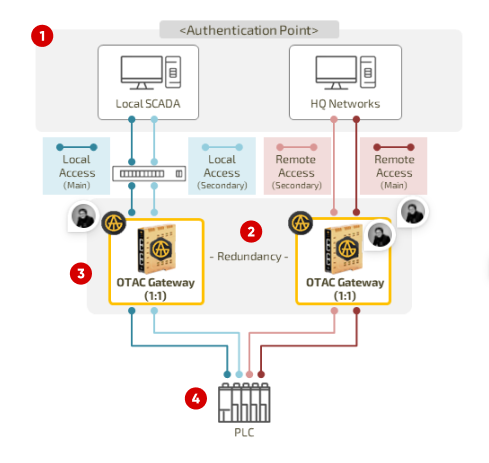
National water treatment infrastructure
Mitigating remote access risks by enforcing authentication across distributed OT environments
1:N model deployment
1:1 model deployment
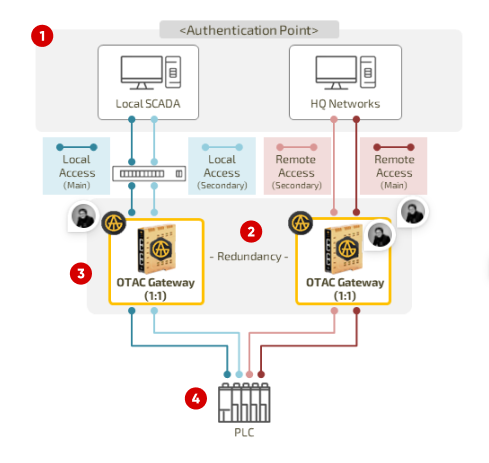
① Access routes through the OTAC Gateway at each local and remote authentication point.
② Configures OTAC Gateway redundancy to ensure stable operation.
③ Applies a blacklist policy — Requires user authentication for endpoint devices registered in the admin portal.
④ Controls user access based on the current infrastructure set-up (1:N and/or 1:1 models)
Compliance-Ready
The OTAC Trusted Access Gateway helps you meet the world’s leading OT cybersecurity regulations:

- NIS2 – Replaces static passwords with dynamic authentication
- NERC CIP – Enforces role-based and multi-factor access
- IEC 62443 – Aligns with FR1: Identification and Authentication Control
- Cyber Resilience Act (CRA) – Ensures secure and auditable access
And by delivering secure endpoint authentication without altering device firmware or requiring internet connectivity, the solution aligns with zero-trust principles for industrial environments.

Contact us today
OTAC Trusted Access Gateway (TAG) FAQs
-
No. The OTAC Trusted Access Gateway integrates seamlessly without altering your current devices or systems.
-
Unlike PKI, OTAC doesn’t require certificate management or bidirectional communication. Each code is generated locally, making it simpler and more resilient in OT environments.
-
Registered smartphones, smart cards or laptops can generate the dynamic codes required for access.
-
No. Codes are generated independently on the user’s device—no network is needed.
-
Yes. The OTAC Trusted Access Gateway provides detailed access logs that include user and device information, improving auditability.
-
Absolutely. It supports compliance with NIS2, IEC 62443, NERC CIP and the Cyber Resilience Act (CRA).
Why swIDch
that provides all of the following features, tested and substantiated
by the University of Surrey technical report
sufficient to IDENTIFY user
and AUTHENTICATION
off-the-network environment
Single-step identification and authentication with the code alone. Include our biometric option and get single-step MFA. Vastly improved UX by removing steps.
OTAC is a dynamic code, which means the code is constantly changing. Eliminates all use of static information. Forget usernames and passwords forever. Vastly reduced workload for IT helpdesks.
No network connection required for generating OTAC, enabling uninterrupted use no matter where you are. No more waiting for additional tokens/OTPs and no need for heavy public key infrastructure (PKI).
Highly configurable code parameters and lightweight SDK/applet means wide range of deployment options on many devices across multiple sectors.
![[swIDch] OTAC TAG-1](https://www.swidch.com/hubfs/%5BswIDch%5D%20OTAC%20TAG-1.jpg)
![[swIDch] OTAC TAG-2](https://www.swidch.com/hubfs/%5BswIDch%5D%20OTAC%20TAG-2.jpg)




