Why OT Security Is Different
- OT systems control physical processes
They run plants, pipelines and production lines not just data. - Downtime has real-world impact
A security failure can stop operations, damage equipment or threaten safety. - Access in OT is inherently risky
Shared accounts and remote access create pathways for attackers into critical systems.
⏰OT security is about who and what can access machines — not just networks and data.


How We Secure OT Access
🔐Built for operational environments
- Designed for industrial networks where connectivity and uptime cannot be assumed.
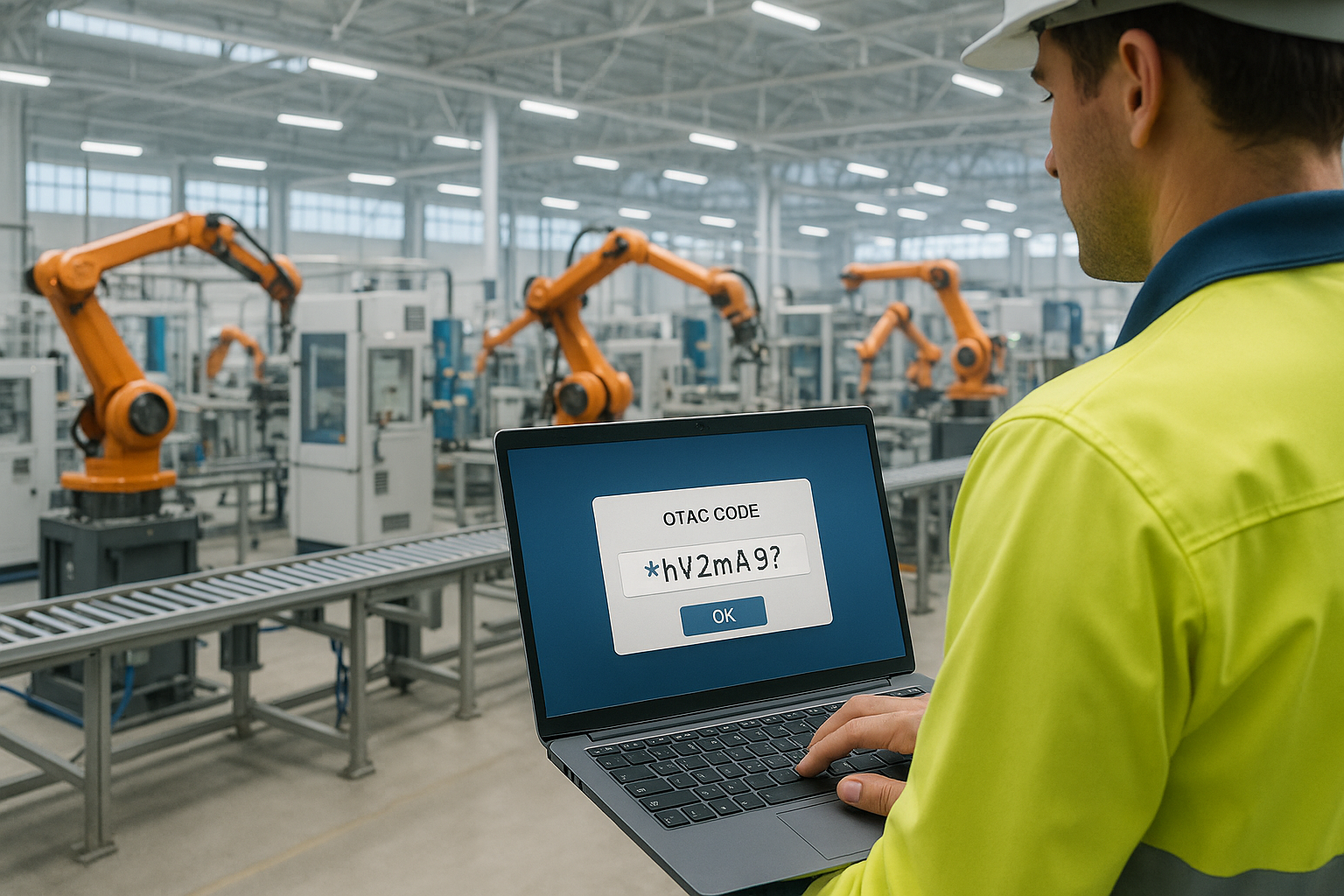
🔢No static credentials
- Dynamic, one-time authentication removes passwords and shared secrets using OTAC (One-Time Authentication Code).
⏱️Security without disrupting operations
- Access protection that fits into OT workflows without adding unnecessary friction.
swIDch At a Glance
350+
Patents and patents
pending worldwide
pending worldwide
50+
Clients Served
14+
Global Acceleration programmes
13+
Global-Scale Awards Won
Award Highlights

Hot Company in Operational Technology (OT) Security at the Top InfoSec Innovator Awards 2024
See More
Explore

The Financial Reality of OT Downtime and the Cost of Authentication Friction
In 2026 downtime in the industrial sector is no
Read More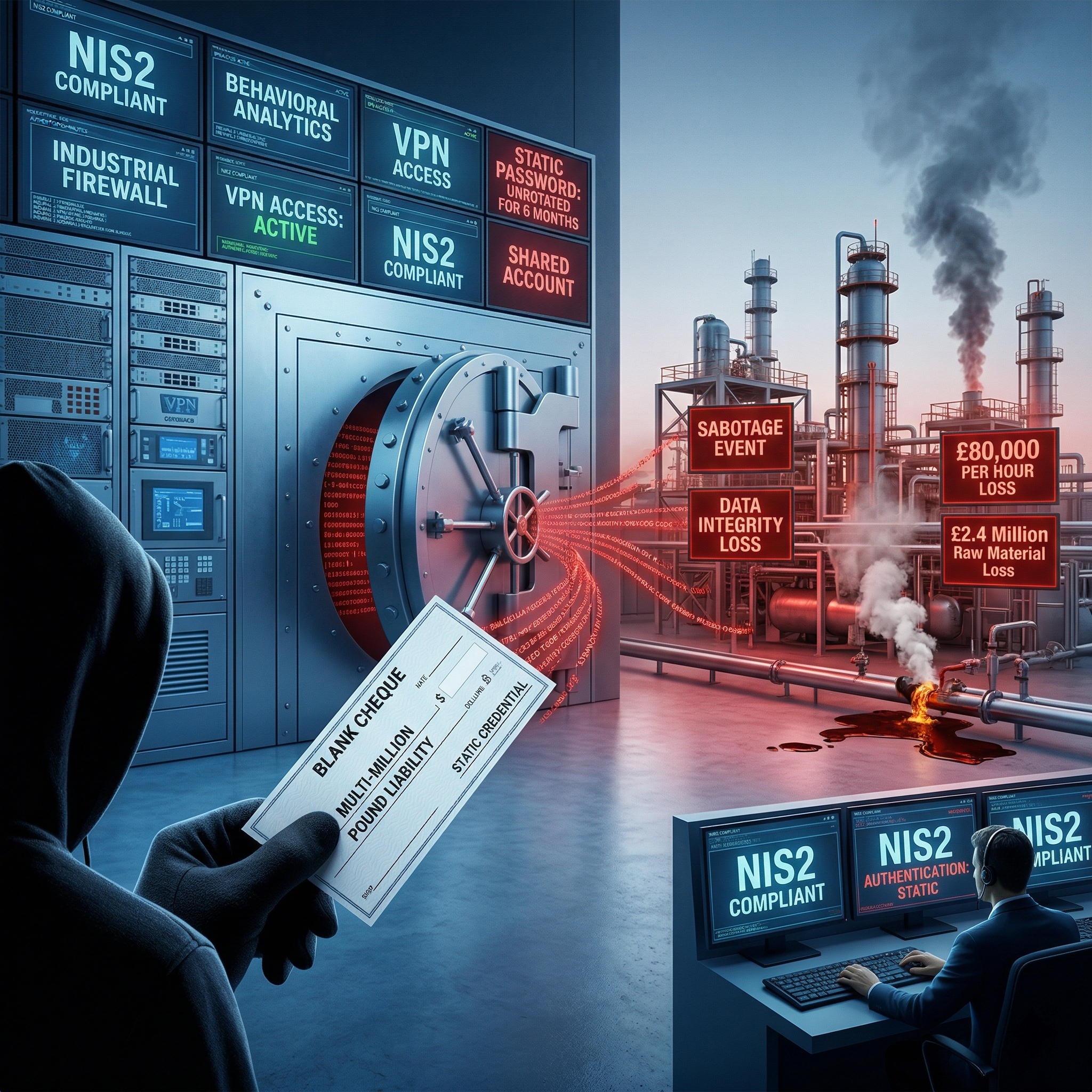
The Blank Cheque Hidden Inside Your OT Security Infrastructure
In 2026 the reliance on static passwords within
Read More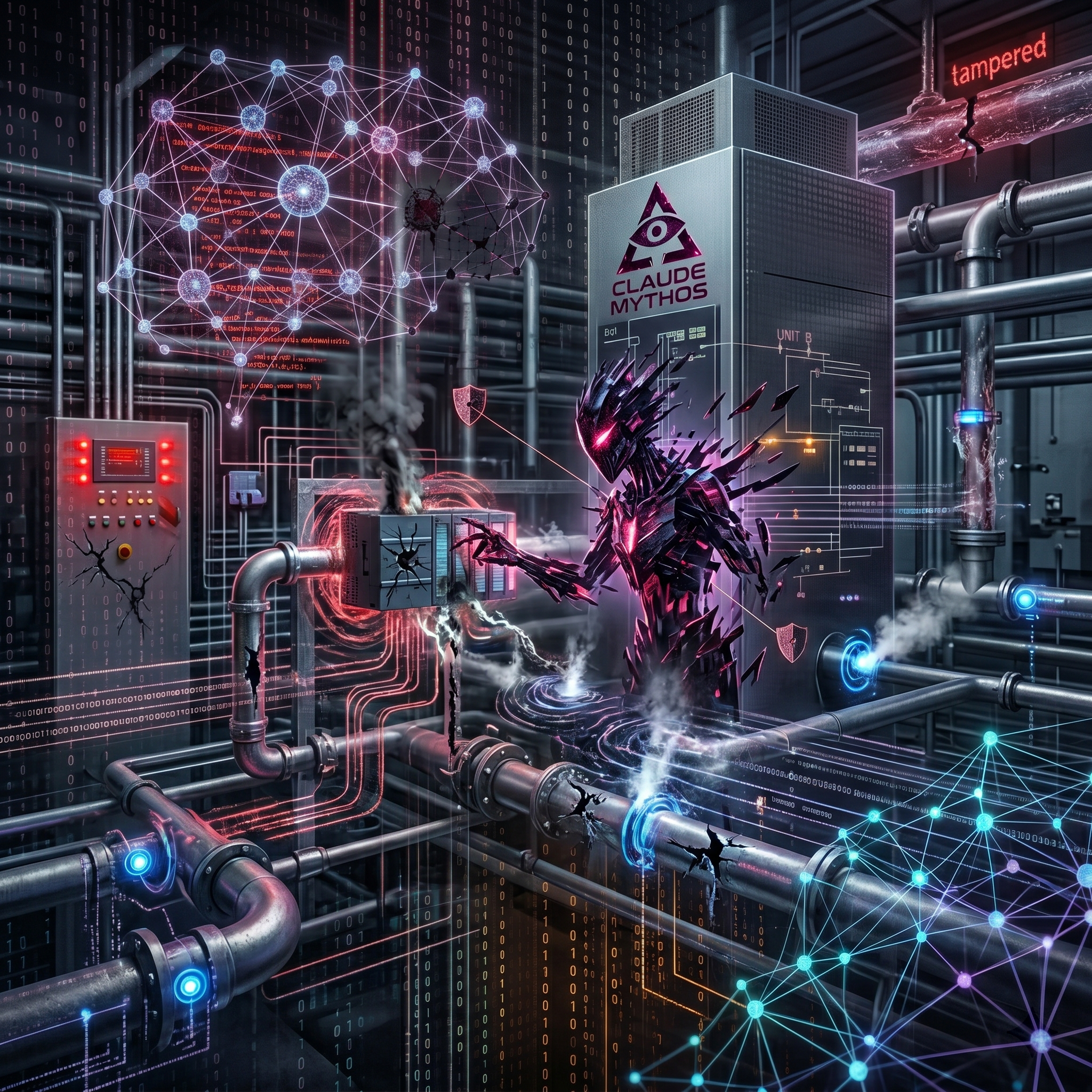
How Claude Mythos democratises industrial cyber attacks
Anthropic's Claude Mythos marks a definitive
Read More