

Military
aircraft, vehicles and forces as friendly.
Pain points
Armed forces are encountered with an ever increasing set of challenges in defending cyber security from the threat of attack due to
a greater dependence on computer systems and a reliance on connected networking. As cyber systems become increasingly interconnected,
a multi-layered and dynamic security system becomes imperative. With increasingly networked systems, the defence sector has been
presented with a whole array of emerging challenges in cyber defence.
Identification Friend or Foe (IFF) is an identification system designed for command and control.
It enables military and civilian air traffic control interrogation systems to identify aircraft, vehicles or forces as friendly
and to determine their bearing and range from the interrogator. Such systems are useful for preventing action against friendly forces.
The military systems on a battlefield must accurately identify potential targets as friend-or-foe when detected within range of available weapon systems.
IIF means that military commanders are repeatedly faced with the onerous decision whether to engage a detected target while avoiding accidental fratricide.
The solution
In the midst of battle, it is very difficult to identify your friendlies or targets.
Current solution to the problem is to identify friendlies from their devices using static information.
OTAC can generate dynamic signals from the device, without the internet.
- Provide unidirectional code generated by the client without communication with the server
- Generate a dynamic code that changes every time and is safe from hacking and leakage
- Block attacks in advance with one-time code that does not allow cloning and spoofing attacks
- Protect devices by issuing a unique code that never overlaps with other connected devices
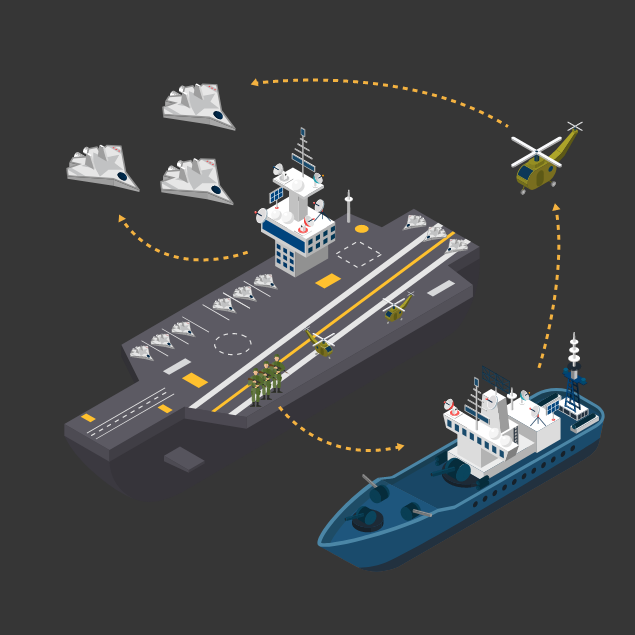
OTAC for IFF
OTAC is a revolutionary authentication technology enabling
such IFF systems to be able to generate a unique,
dynamic and random value without a network, to verify such
values, and identify targets in one simple unidirectional process.
OTAC sends a one-way code to help identify allies,
transmits a random code to prevent unauthorized use due to
enemy signal hijacking, and ensures the safety of allies
by generating an identifiable code even in the off-the-network environment.
See our Drone solution page for example use cases
Why swIDch
that provides all of the following features, tested and substantiated
by the University of Surrey technical report
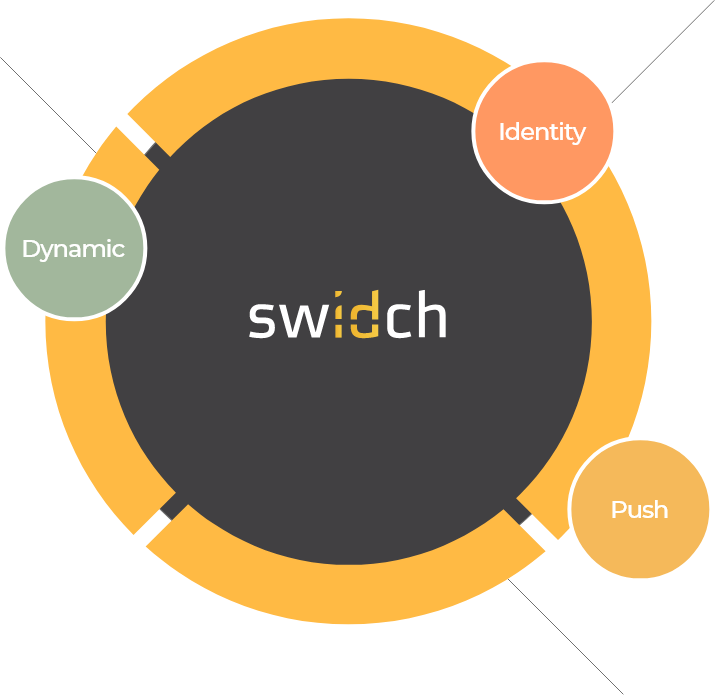
sufficient to IDENTIFY user
and AUTHENTICATION
off-the-network environment
Single-step identification and authentication with the code alone. Include our biometric option and get single-step MFA. Vastly improved UX by removing steps.
OTAC is a dynamic code, which means the code is constantly changing. Eliminates all use of static information. Forget usernames and passwords forever. Vastly reduced workload for IT helpdesks.
No network connection required for generating OTAC, enabling uninterrupted use no matter where you are. No more waiting for additional tokens/OTPs and no need for heavy public key infrastructure (PKI).
Highly configurable code parameters and lightweight SDK/applet means wide range of deployment options on many devices across multiple sectors.